
Comprehensive data protection used to rely on perimeter controls, encryption, and backup, but that model crumbles in today’s reality. Sensitive data now moves constantly across cloud, SaaS, and hybrid environments, accessed by humans and AI and reshaped at scale under growing regulatory pressure. Protecting data requires a coordinated system of continuous visibility, governance, monitoring, and response.
Data Security Posture Management (DSPM)
Build every data security decision on facts, not assumptions, with always-on visibility into your sensitive data and its true risk posture.
Reveals clearly and accurately:

What sensitive data you have, where it lives, and how sensitive it really is

Security posture of all sensitive and regulated data

Who can access it across cloud, SaaS, and hybrid environments
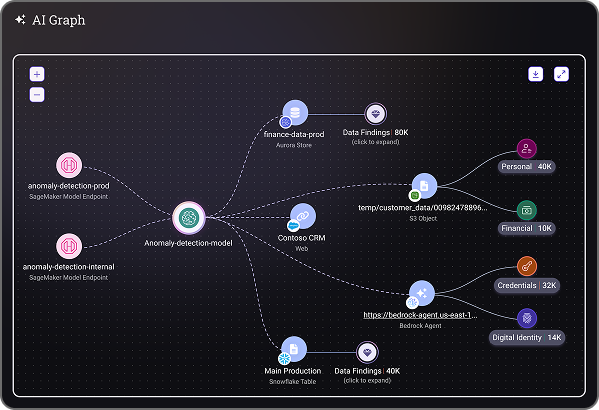
DSPM for AI: Governing Risk at Machine Speed
Govern AI data risk at machine speed by knowing exactly what AI can see, tightening its access, and enforcing guardrails without slowing adoption.
Empower AI security teams to:

Map which datasets AI systems can access and where access is overpermissioned

Enforce guardrails on sensitive data usage

Enable safe AI adoption without slowing innovation and productivity
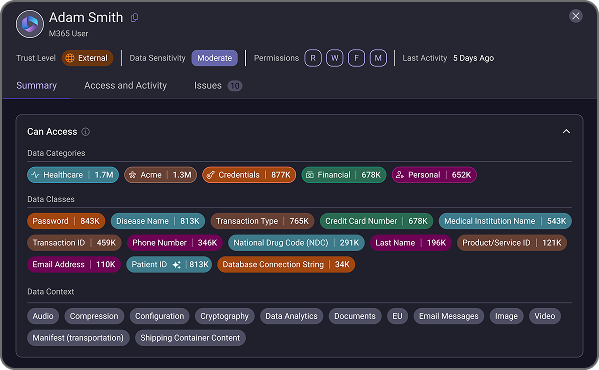
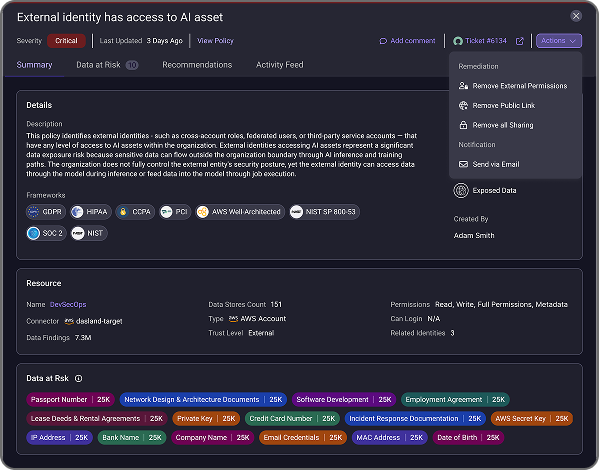
Data Access Governance (DAG): From Visibility to Control
Turn data sensitivity into precise, enforceable access controls that shrink blast radius long before incidents happen.
Command data access with precision to:

Eliminate over-privileged access for users, apps, and AI identities

Detect toxic permission combinations that create high-risk data

Enforce least privilege at scale to reduce blast radius before incident occurs
Data Detection and Response (DDR): Stopping Risk in Motion
Static tools show where risk might exist. DDR shows when risk is actually happening, so teams can act before exposure escalates.
Spot and stop live data threats by:

Detection of anomalous or risky access that signal misuse of sensitive data

Identification of potential exfiltration paths and risky data flows

Real-time visibility that accelerates investigation and response

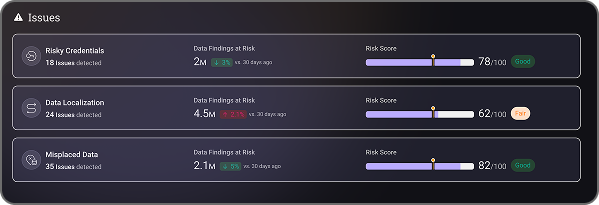
Automated Remediation: Proving Risk Is Reduced
Go beyond just finding issues. Prove risk is actually reduced with automated, impact-based remediation that closes the loop.
Drive fast, effective remediation by:

Prioritizing based on data sensitivity, exposure conditions, and who can access the data

Factoring business and regulatory impact into every decision

Automating, validating, and closing remediation to prove real risk reduction
%201.png)