Data Security Posture Management (DSPM): A Complete Guide
What is DSPM?
DSPM or Data Security Posture Management is an approach to securing cloud data by ensuring that data assets always have the correct security posture, regardless of where it’s been duplicated or moved to in your public cloud.
DSPM ensures data security posture stays strong and adaptable, following data wherever it's stored or moved.
It does this by:
- Discovering all the data in your public cloud environment - including shadow data that’s been created but isn’t used or monitored.
- Understanding the right security measures needed for different types of data.
- Prioritizing alerts by how sensitive the data is and providing practical solutions.
Unlike traditional tools that just find sensitive data, DSPM goes further. It not only identifies data but also assesses its importance for the business and its specific security requirements, helping security teams respond more effectively to potential threats.
For example, let’s say a data discovery tool finds PII data. You wouldn’t need an alert if it has the proper security posture. A good DSPM solution wouldn’t waste your time with one.
Read more about different DSPM use cases.
{TOC}
What are the Key Features of DSPM?
For IT and security professionals, grasping the features of Data Security Posture Management is essential for modernizing data protection strategies. As organizations increasingly rely on cloud environments, traditional security measures fall short. DSPM addresses this gap by providing a systematic approach to data security across all environments — cloud and on-premises. Understanding the components below will equip you with the knowledge to implement more effective data discovery, accurate data classification, apply appropriate security measures, prioritize exception alerts based on data sensitivity, and deploy practical solutions for risk mitigation. This insight is crucial for enhancing your organization's security posture and ensuring compliance in today's complex data landscape.
Data Discovery & Classification
DSPM goes beyond detecting standard data like social security numbers. It leverages machine learning to identify complex data types such as intellectual property, and does so for unstructured stores that often represent visibility gaps, surpassing traditional data analysis methods. Additionally, DSPM integrates with data catalogs for ownership tracking and is scalable for analyzing large data volumes in cloud environments.
DSPM’s discovery and classification capabilities are as follows:
- Broad Identification: DSPM discovers and accurately classifies both structured and unstructured data.
- Advanced Analysis: DSPM uses machine learning for deeper contextual data insights.
- Efficient and Scalable: DSPM effectively handles large amounts of data to thoroughly identify sensitive information.
- Shadow Data Discovery: DSPM finds all data automatically - known and unknown (shadow data).
Exposure & Risk Assessment
Begin by identifying and evaluating potential security risks and vulnerabilities within your system. Continuously scan data stores and new data for proper posture to detect weak points (often, data that moves can lose the protections it once had). Implement both qualitative and quantitative risk assessment methodologies to thoroughly analyze and address any security threats. This comprehensive approach ensures a robust defense against potential security breaches.
Access Governance
Data sharing and collaboration in the cloud is an essential element driving the business forward, however, it opens organizations up to a host of data access risks. Data moves and flows dynamically, and often ends up in places without proper access controls.
As a result, the authorization gap continues to grow, widening the divide between what data users and applications can access and what they should have access to, based on least privileges and zero trust approaches.
Incident Response & Remediation
Effectively plan and manage security incidents by adhering to established incident response frameworks such as NIST SP 800-61. Integrate Security Information and Event Management (SIEM) systems to enhance your incident response capabilities. This structured approach ensures swift identification, assessment, and remediation of security incidents, minimizing potential damage and ensuring a rapid recovery.
Compliance and Audit Management
Ensure compliance with relevant regulations and maintain readiness for audits by automating compliance checks and regularly generating compliance reports. Efficiently manage audit logs to track and document all activities. This structured approach helps maintain regulatory adherence and simplifies the audit process, ensuring your organization meets all necessary standards.
Continuous Monitoring & Threat Intelligence
Maintain constant surveillance of systems and stay updated on evolving threats by implementing Security Information and Event Management (SIEM) solutions. Utilize threat intelligence feeds and perform thorough analyses to detect and respond to potential security issues. This proactive approach ensures that your organization remains vigilant and well-prepared against emerging cyber threats.
DSPM and Emerging Technologies
Integration with AI and Machine Learning for Enhanced Data Protection
Sentra’s classification technology supports both structured data and unstructured data. For structured data we use advanced statistical analysis to determine column-level classification with accuracy, while for unstructured data we use LLMs and ML to accurately understand the context of data and classify it. Using multiple technologies depending on the data helps to reduce processing resource consumption (reducing cloud spend) and leads to a more accurate result with low false positives.
DSPM in the Context of Edge Computing (SASE) and DLP
Organizations rely on SASE and Endpoint DLP solutions to prevent data breaches by identifying and protecting common types of sensitive information, such as credit card numbers and PII. These identify and alert when sensitive data like credit card information or social security numbers, is being moved outside of the organization's control. Over time, organizations often struggle to identify certain types of sensitive data. SASE and DLP lack sensitivity of data based on its specific context within the organization, such as customer data or intellectual property. This limitation leaves critical data vulnerable, highlighting the need for advanced and more effective methods to accurately classify and secure all types of sensitive information.
Why are Cloud-First Enterprises Adopting DSPM?
Cloud-first enterprises prioritize cloud adoption for its scalability, availability, and data redundancy, enabling agile responses to market changes and bolstering overall resilience.
Progressive organizations realize the value that data brings — with its potential to unleash untapped revenue opportunities. Innovators (BI analysts, developers, etc.) can utilize data to find hidden trends and buying patterns, model and test new application and user experiences, or segment markets for targeted offerings or promotions. Sharing and collaborating across varied teams (i.e. data democratization) facilitates this rapid exploration and invention.
Cloud has made this rapid innovation possible as it is quicker to deploy/invoke, requires little staff to maintain, and is much more agile to scale to meet dynamic business needs. However, security hasn’t always been able to keep pace and follow along - creating exposures along the way. Data that is easily replicated, moved to new environments (ex. Production data move to a development environment), or shared extensively may lack originally intended security controls to protect it. This is where DSPM comes in.
The adoption of DSPM further strengthens data security within cloud environments, closely aligning with the priorities of cloud-first enterprises.
Here's how:
- Enhanced Data Security: Improves data security in cloud environments, ensuring sensitive information remains protected across distributed infrastructures, a crucial requirement for cloud-first enterprises.
- Comprehensive Data Protection: Offers comprehensive data protection by actively tracking sensitive data throughout its lifecycle, addressing security concerns at scale.
- Dynamic Security Approach: Unlike static methods, dynamically secures sensitive data, even during duplication or movement, fitting the dynamic nature of cloud-first enterprises.
- Enhanced Visibility and Risk Assessment: Provides automatic visibility, risk assessment, and access analysis for cloud data, ensuring continuous security monitoring.
- Contextual Insights: Complements traditional security practices by offering rich contextual information based on data sensitivity, enhancing overall security strategies.
In essence, DSPM emerges as a critical component of cloud-first strategies, aligning closely with the priorities of enterprises seeking robust data security measures in dynamic cloud environments
When Should Your Organization Consider Using DSPM Solutions?
Consider using DSPM tools for your organization when:
- Operating in a multi-cloud environment with varying security measures.
- Frequently replicating and moving data for testing, backup, or disaster recovery.
- Dealing with a large user base and complex access control requirements.
- Needing to comply with strict data protection regulations.

What to Look for in a DSPM Solution?
When choosing a DSPM solution, it's important to analyze certain capabilities that are crucial for effective data security management in your organization:
How to Implement Data Security Posture Management
Now that you're familiar with DSPM and its importance for your organization, let's move to the practical part: implementing it. We've simplified the process into clear, manageable steps to make DSPM implementation straightforward.
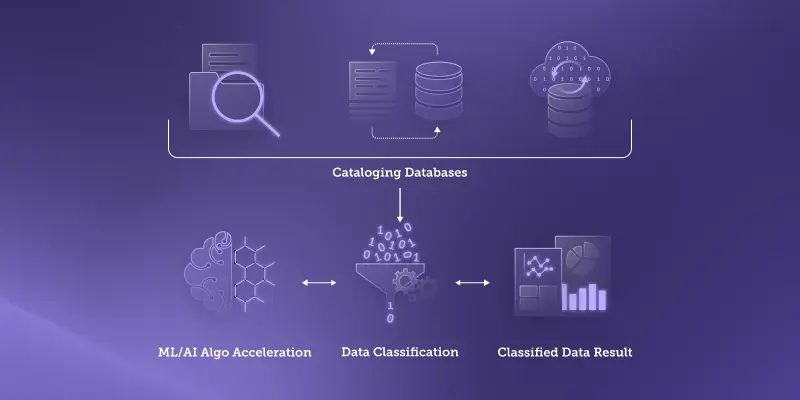
Step 1: Discovery
This foundational phase is about gaining a clear picture of your data landscape.
- It involves a thorough mapping of all data assets, identifying various data sources, and cataloging databases.
- The challenge here is managing both structured and unstructured data spread across different platforms.
- Classifying data based on sensitivity and importance is key, with AI and machine learning providing a significant edge in this process.
Step 2: Assessment
Focusing on your data's security posture, this step is about understanding where you stand.
- You'll need to review existing security measures and pinpoint any vulnerabilities.
- As threats evolve, this becomes an ongoing effort to ensure your data security is always up to standard.

Step 3: Remediation
Now comes the proactive part: addressing the risks you've identified.
- Implementing solutions like data encryption, refining access controls, and updating software are typical strategies.
- This phase combines tech solutions with strategic human insight, making the role of your security team crucial.

Challenges and Solutions in Implementing DSPM
Implementing DSPM is essential but can be complex due to various challenges. Below is a table outlining common challenges and how to effectively overcome them:
Tips for Implementing DSPM
Implementing DSPM requires meticulous planning, strategic vision, and ongoing commitment. The key lies in striking the optimum balance between automated and manual controls, between prevention and detection strategies, and between flexibility and rigidity of security protocols.
1. Centralized Security Management
Centralized management is crucial for a robust DSPM strategy. It involves aggregating, correlating, and analyzing security data from across the organization in one place. This approach enhances visibility into security postures, reduces fragmentation of controls, and facilitates quicker response times.
2. Continuous Monitoring
Maintaining a strong security posture requires continuous commitment. Regular auditing, real-time monitoring, and proactive threat hunting are essential in staying ahead of evolving threats. Automated monitoring tools assist in tracking deviations from the desired posture, while anomaly detection algorithms identify unusual activity or patterns.
3. Intelligent Alerting
Establishing an intelligent alerting system helps separate the signal from unwanted noise, reducing the chances of alert fatigue. Incorporating machine learning algorithms improves the alerting system's accuracy and efficiency over time.
4. Automated Remediation
Automated remediation tools offer instant reactions to known threats, reducing the window of exposure. This automation not only allows for quicker response times but also reduces the manual workload, freeing up the security team to focus on more complex issues.
5. Regular Training and Awareness Programs
Regular training programs for employees prevent avoidable security breaches by fostering a culture of security, enhancing understanding of security protocols, and reducing susceptibility to social engineering attacks.
What's the Difference Between CSPM and DSPM?
Cloud Security Posture Management (CSPM) solutions secure cloud infrastructure, while DSPM focuses on cloud data. CSPM identifies vulnerabilities in resources like VMs and VPC networks, with some basic data insights. However, it often lacks data sensitivity prioritization.
DSPM targets data vulnerabilities such as overexposure, access controls, and anomalies, bridging data with infrastructure security.
This allows teams to grasp at-risk sensitive data instead of just listing vulnerabilities.
Read more about DSPM vs. CSPM.
Conclusion
In summary, Data Security Posture Management (DSPM) plays a crucial role in addressing the complex security challenges posed by cloud migration. By ensuring that security measures adapt alongside data movements in the cloud, DSPM effectively mitigates risks related to data replication and movement.
Moreover, DSPM offers a comprehensive approach to data security, empowering organizations to maintain control and visibility over their data assets across diverse cloud environments. With DSPM in place, businesses can proactively protect their valuable data from potential threats, enhancing their overall security posture in the dynamic landscape of cloud computing.
What is the difference between DSPM and DLP?
Data Loss Prevention (DLP) focuses on preventing unauthorized data exposure or leakage, while Data Security Posture Management (DSPM) takes a broader approach, covering the entire lifecycle of data.
Here are the main differences:
DLP (Data Loss Prevention):
- Prevents unauthorized data exposure or leakage.
- Utilizes content analysis and policy enforcement to minimize data risks and mitigate potential data breaches.
- Monitors data in motion, at rest, and in use to prevent unauthorized access.
DSPM (Data Security Posture Management):
- Manages data access, classification, encryption, and user behavior.
- Aims to protect data holistically throughout its lifecycle, reducing the likelihood of data breaches.
- Emphasizes prevention of unauthorized access and misuse to mitigate data security risks.
What is a data security platform?
A Data Security Platform is a solution designed to strengthen data protection measures within organizations.
It incorporates various features:
- Data Discovery: Identifying sensitive data across diverse systems and repositories.
- Data Classification: Categorizing data based on its sensitivity for targeted protection.
- Data Loss Prevention (DLP): Preventing unauthorized data exposure or leakage.
- Encryption: Implementing techniques to protect data in transit and at rest.
- Access Control: Managing user permissions to ensure data is accessible only to authorized individuals.
- User Behavior Analytics: Monitoring user activities for detecting unusual patterns.
- Threat Detection: Identifying potential security and data breaches and anomalies in real-time.
- Compliance Management: Ensuring data security practices align with industry regulations.
What is a Security Posture?
A security posture reflects an organization's holistic approach to cybersecurity, covering strategies and practices to defend against cyber threats effectively. Key components include:
- Risk Management: Identifying, assessing, and addressing potential risks to assets and data.
- Security Policies: Establishing guidelines and protocols to govern security practices.
- Access Controls: Managing resource and data access to minimize vulnerabilities.
- Threat Detection: Using tools and practices to identify and respond to security threats.
- Incident Response: Developing procedures to handle and recover from security incidents.
- Employee Training: Educating personnel on security best practices and potential risks.
- Compliance Measures: Ensuring compliance with industry regulations and standards.
- Regular Assessments: Evaluating security measures regularly for effectiveness.
A strong security posture integrates these elements to proactively protect an organization's digital assets, infrastructure, and sensitive information from a wide range of cyber threats.
What is the difference between DSPM and CASB?
DSPM manages data security in cloud environments, ensuring protection against breaches. CASB acts as a bridge between users and cloud services, enforcing security policies and monitoring activity. While DSPM focuses on data protection, CASB enhances overall cloud security.
Is DSPM part of Cnapp?
No, DSPM (Data Security Posture Management) is not a component of Cnapp (Cloud Native Application Protection Platform). While Cnapp focuses on securing cloud-native applications, DSPM is dedicated to managing and securing cloud data. However, integrating both solutions can bolster overall cloud security posture.
Can DSPM Fit into Broader Security Strategies?
Absolutely. DSPM not only supports traditional security methods but also enriches them with valuable insights tailored to data sensitivity. It ensures continuous security for cloud data by offering automatic visibility, risk assessment, and access analysis, addressing the unique challenges of cloud data management







