- No data is copied outside your environment.
- More secure by design.
- Compliance built in, not bolted on.
- Lower total cost of ownership.
- Highest scalability.
Product Overview
Your AI stack has three layers.
AI Data Readiness layer is missing.
You've invested in AI infrastructure and governance. Without data readiness, both run blind. Sentra is the layer that makes them work.
01
AI Infrastructure Layer
Models, pipelines, GPUs, deployment. The layer that got funded first.
02
AI Governance Layer
Guardrails for AI behavior. Blind to the data underneath.
AI Data Readiness Layer
Continuous discovery, classification, hygiene, and access governance — at petabyte scale, in your environment. The missing layer AI has been running without.
The Sentra Platform for Continuous AI Data Readiness and Governance
The Sentra Platform for Continuous AI Data Readiness and Governance
Sentra’s Breakthrough
Data Security Architecture
Data security that lives in your environment — not ours.
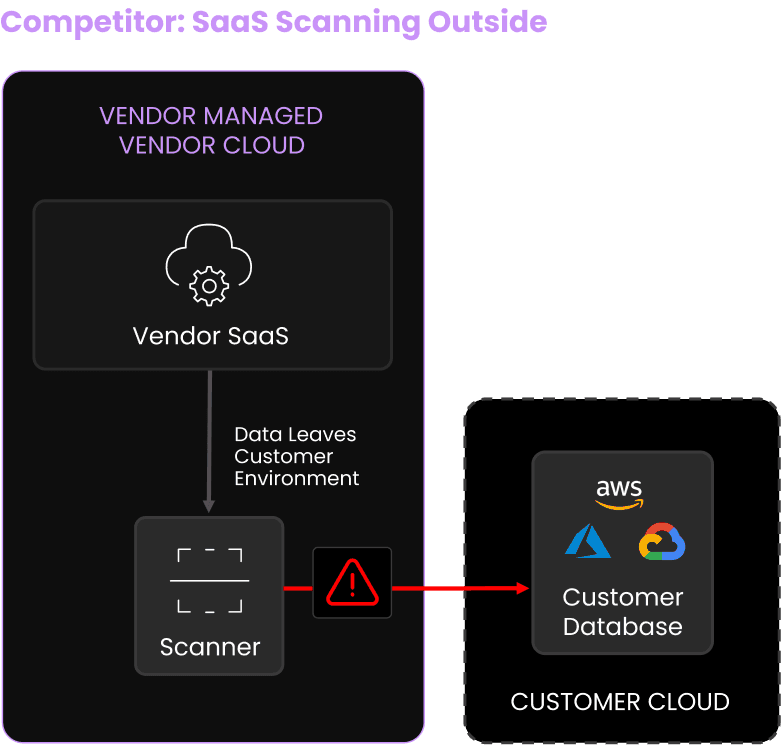
- BAD: All data is copied to vendor.
- Vendor has access to all sensitive data from the customer.
- Not suitable for regulated data.
- Low scalability.
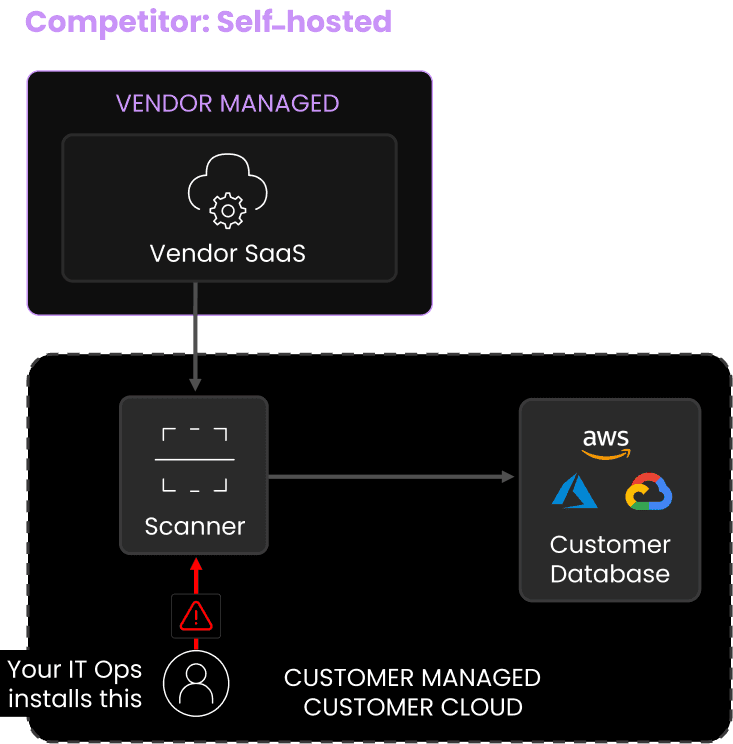
- Cost prohibitive (labor + operations).
- Requires a manual deployment in every region.
- Each deployment requires ongoing maintenance.
- Low scalability.
Sentra Wins Fortune 500 Customer Bake-off
Scalability
Accuracy
Operational Cost Efficiency
9 PB scanned
<72 hrs
>98%
<1% FPs/FNs
~$40,000 /yr
to scan 100 PB
A Top Emerging DSPM Vendor
1 PB scan failed
~60 hrs
<93%
>5% FPs/FNs
$400,000+ /yr
to scan 100 PB
Data security with measurable business impact.
The ROI numbers that matter
ROI
~6x
Return on investment
$5.76M in quantified 3-year benefits against ~$955K in total costs — before NPV is finalized.
Labor savings
90%
Less manual governance work
7 FTEs reclaimed from manual oversight. $3M saved over 3 years. Risk focus, not data wrangling.
Compliance
94%
Reduction in DLP coverage scope
DLP scope drops from
3,500 to 210 employees. $329K saved annually, plus 1 FTE freed from false-positive triage.
Cloud costs
$375K
Avoided cloud spend per year
Shadow data visibility reclaims 1.5% of cloud spend. One customer cut 110 databases worth $1.1M/year.
Resources
AI-ready data is the new competitive advantage.
AI is Live.
Your data readiness and governance isn’t.
Sentra discovers, classifies, and governs every dataset
AI can touch—from Copilot to Bedrock—at petabyte scale.