Secure AI Adoption for Enterprise Data Protection: Are You Prepared?
In today’s fast-moving digital landscape, enterprise AI adoption presents a fascinating paradox for leaders: AI isn’t just a tool for innovation; it’s also a gateway to new security challenges. Organizations are walking a tightrope: Adopt AI to remain competitive, or hold back to protect sensitive data.
With nearly two-thirds of security leaders even considering a ban on AI-generated code due to potential security concerns, it’s clear that this tension is creating real barriers to AI adoption.
A data-first security approach provides solid guarantees for enterprises to innovate with AI safely. Since AI thrives on data - absorbing it, transforming it, and creating new insights - the key is to secure the data at its very source.
Let’s explore how data security for AI can build robust guardrails throughout the AI lifecycle, allowing enterprises to pursue AI innovation confidently.
Data Security Concerns with AI
Every AI system is only as strong as its weakest data link. Modern AI models rely on enormous data sets for both training and inference, expanding the attack surface and creating new vulnerabilities. Without tight data governance, even the most advanced AI models can become entry points for cyber threats.
How Does AI Store And Process Data?
The AI lifecycle includes multiple steps, each introducing unique vulnerabilities. Let’s consider the three main high-level stages in the AI lifecycle:
- Training: AI models extract and learn patterns from data, sometimes memorizing sensitive information that could later be exposed through various attack vectors.
- Storage: Security gaps can appear in model weights, vector databases, and document repositories containing valuable enterprise data.
- Inference: This prediction phase introduces significant leakage risks, particularly with retrieval-augmented generation (RAG) systems that dynamically access external data sources.
Data is everywhere in AI. And if sensitive data is accessible at any point in the AI lifecycle, ensuring complete data protection becomes significantly harder.
AI Adoption Challenges
Reactive measures just won’t cut it in the rapidly evolving world of AI. Proactive security is now a must. Here’s why:
- AI systems evolve faster than traditional security models can adapt.
New AI models (like DeepSeek and Qwen) are popping up constantly, each introducing novel attack surfaces and vulnerabilities that can change with every model update..
Legacy security approaches that merely react to known threats simply can't keep pace, as AI demands forward-thinking safeguards.
- Reactive approaches usually try to remediate at the last second.
Reactive approaches usually rely on low-latency inline AI output monitoring, which is the last step in a chain of failures that lead to data loss and exfiltration, and the most challenging position to prevent data-related incidents.
Instead, data security posture management (DSPM) for AI addresses the issue at its source, mitigating and remediating sensitive data exposure and enforcing a least-privilege, multi-layered approach from the outset.
- AI adoption is highly interoperable, expanding risk surfaces.
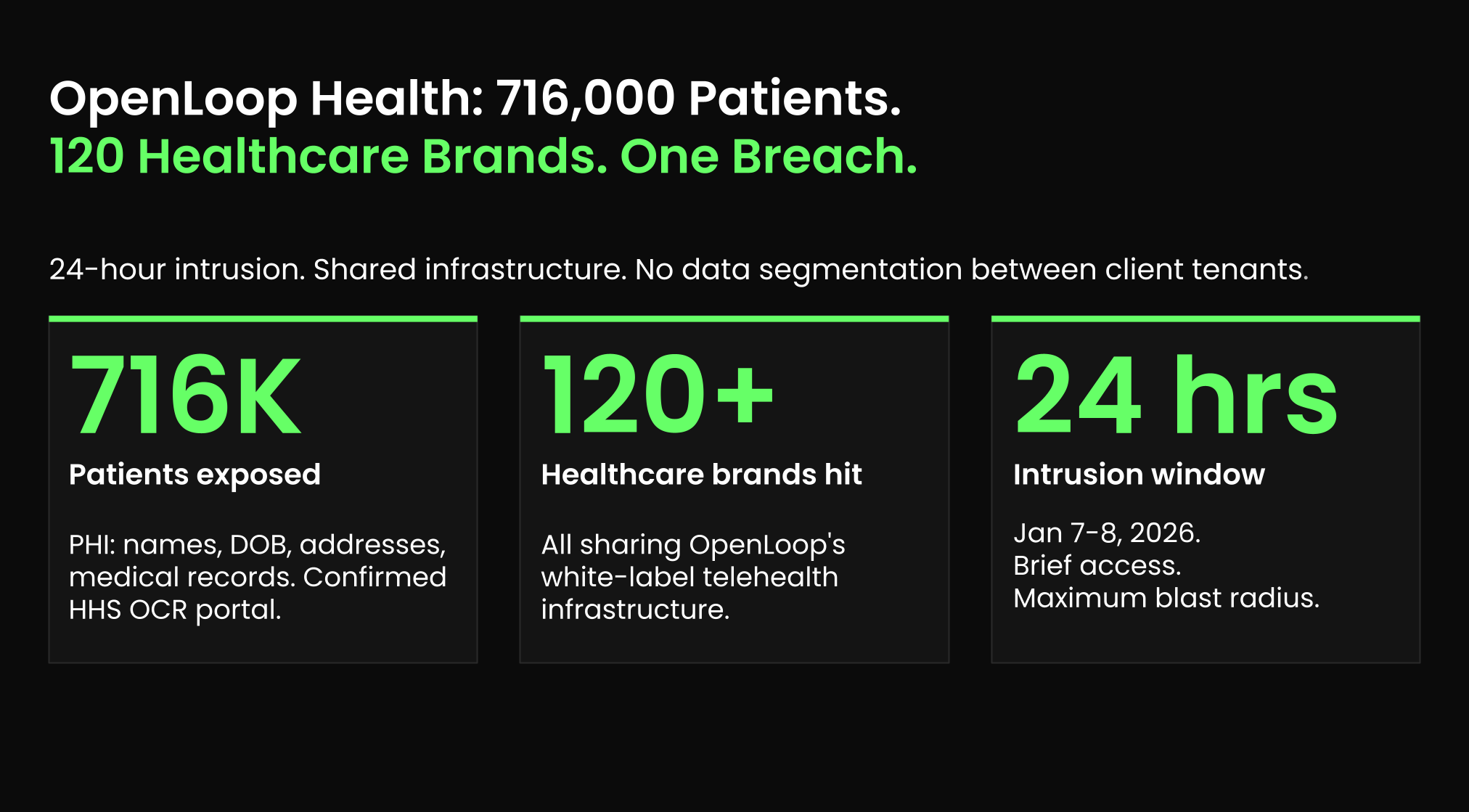
Most enterprises now integrate multiple AI models, frameworks, and environments (on-premise AI platforms, cloud services, external APIs) into their operations. These AI systems dynamically ingest and generate data across organizational boundaries, challenging consistent security enforcement without a unified approach.
Traditional security strategies, which only respond to known threats, can’t keep pace. Instead, a proactive, data-first security strategy is essential. By protecting information before it reaches AI systems, organizations can ensure AI applications process only properly secured data throughout the entire lifecycle and prevent data leaks before they materialize into costly breaches.
Of course, you should not stop there: You should also extend the data-first security layer to support multiple AI-specific controls (e.g., model security, endpoint threat detection, access governance).
What Are the Security Concerns with AI for Enterprises?
Unlike conventional software, AI systems continuously learn, adapt, and generate outputs, which means new security risks emerge at every stage of AI adoption. Without strong security controls, AI can expose sensitive data, be manipulated by attackers, or violate compliance regulations.
For organizations pursuing AI for organization-wide transformation, understanding AI-specific risks is essential:
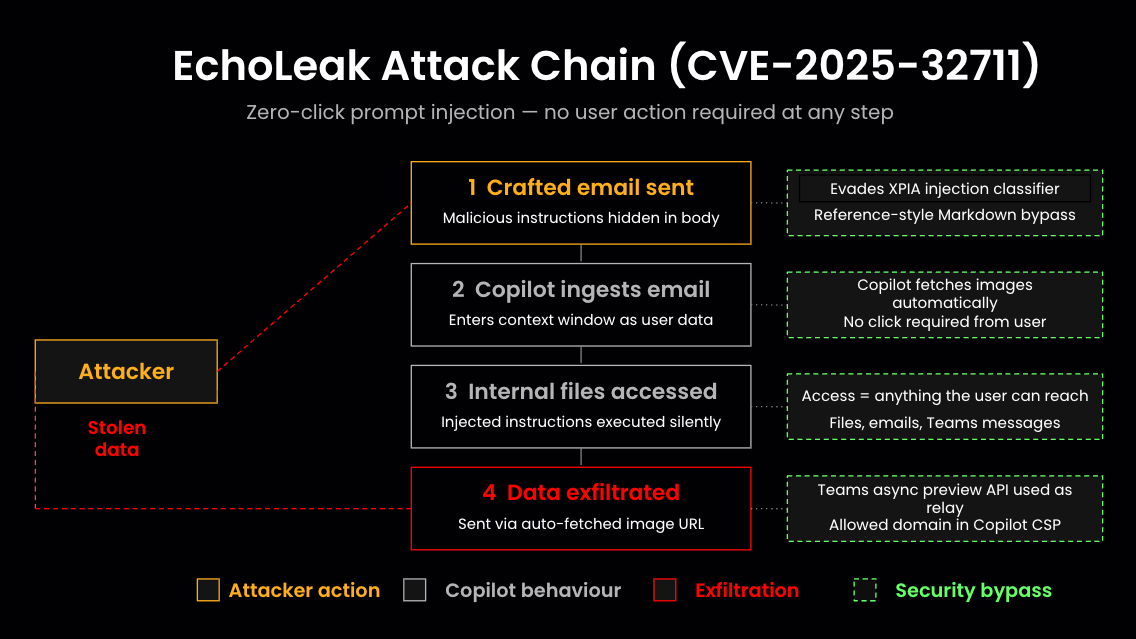
- Data loss and exfiltration: AI systems essentially share information contained in their training data and RAG knowledge sources and can act as a “tunnel” through existing data access governance (DAG) controls, with the ability to find and output sensitive data that the user is not authorized to access.
In addition, Sentra’s rich best-of-breed sensitive data detection and classification empower AI to perform DLP (data loss prevention) measures autonomously by using sensitivity labels.
- Compliance & privacy risks: AI systems that process regulated information without appropriate controls create substantial regulatory exposure. This is particularly true in heavily regulated sectors like healthcare and financial services, where penalties for AI-related data breaches can reach millions of dollars.
- Data poisoning: Attackers can subtly manipulate training and RAG data to compromise AI model performance or introduce hidden backdoors, gradually eroding system reliability and integrity.
- Model theft: Proprietary AI models represent significant intellectual property investments. Inadequate security can leave such valuable assets vulnerable to extraction, potentially erasing years of AI investment advantage.
- Adversarial attacks: These increasingly prevalent threats involve strategic manipulations of AI model inputs designed to hijack predictions or extract confidential information. Adequate machine learning endpoint security has become non-negotiable.
All these risks stem from a common denominator: a weak data security foundation allowing for unsecured, exposed, or manipulated data.
The solution? A strong data security posture management (DSPM) coupled with comprehensive visibility into the AI assets in the system and the data they can access and expose. This will ensure AI models only train on and access trusted data, interact with authorized users and safe inputs, and prevent unintended exposure.
AI Endpoint Security Risks
Organizations seeking to balance innovation with security must implement strategic approaches that protect data throughout the AI lifecycle without impeding development.
Choosing an AI security solution: ‘DSPM for AI’ vs. AI-SPM
When evaluating security solutions for AI implementation, organizations typically consider two primary approaches:
- Data security posture management (DSPM) for AI implements data-related AI security features while extending capabilities to encompass broader data governance requirements. ‘DSPM for AI’ focuses on securing data before it enters any AI pipeline and the identities that are exposed to it through Data Access Governance. It also evaluates the security posture of the AI in terms of data (e.g., a CoPilot with access to sensitive data, that has public access enabled).
- AI security posture management (AI-SPM) focuses on securing the entire AI pipeline, encompassing models and MLOps workflows. AI-SPM features include AI training infrastructure posture (e.g., the configuration of the machine on which training runs) and AI endpoint security.
While both have merits, ‘DSPM for AI’ offers a more focused safety net earlier in the failure chain by protecting the very foundation on which AI operatesーdata. Its key functionalities include data discovery and classification, data access governance, real-time leakage and anomalous “data behavior” detection, and policy enforcement across both AI and non-AI environments.
Best Practices for AI Security Across Environments
AI security frameworks must protect various deployment environments—on-premise, cloud-based, and third-party AI services. Each environment presents unique security challenges that require specialized controls.
On-Premise AI Security
On-premise AI platforms handle proprietary or regulated data, making them attractive for sensitive use cases. However, they require stronger internal security measures to prevent insider threats and unauthorized access to model weights or training data that could expose business-critical information.
Best practices:
- Encrypt AI data at multiple stages—training data, model weights, and inference data. This prevents exposure even if storage is compromised.
- Set up role-based access control (RBAC) to ensure only authorized parties can gain access to or modify AI models.
- Perform AI model integrity checks to detect any unauthorized modifications to training data or model parameters (protecting against data poisoning).
Cloud-Based AI Security
While home-grown cloud AI services offer enhanced abilities to leverage proprietary data, they also expand the threat landscape. Since AI services interact with multiple data sources and often rely on external integrations, they can lead to risks such as unauthorized access, API vulnerabilities, and potential data leakage.
Best practices:
- Follow a zero-trust security model that enforces continuous authentication for AI interactions, ensuring only verified entities can query or fine-tune models.
- Monitor for suspicious activity via audit logs and endpoint threat detection to prevent data exfiltration attempts.
- Establish robust data access governance (DAG) to track which users, applications, and AI models access what data.
Third-Party AI & API Security
Third-party AI models (like OpenAI's GPT, DeepSeek, or Anthropic's Claude) offer quick wins for various use cases. Unfortunately, they also introduce shadow AI and supply chain risks that must be managed due to a lack of visibility.
Best practices:
- Restrict sensitive data input to third-party AI models using automated data classification tools.
- Monitor external AI API interactions to detect if proprietary data is being unintentionally shared.
- Implement AI-specific DSPM controls to ensure that third-party AI integrations comply with enterprise security policies.
Common AI implementation challenges arise when organizations attempt to maintain consistent security standards across these diverse environments. For enterprises navigating a complex AI adoption, a cloud-native DSPM solution with AI security controls offers a solid AI security strategy.
The Sentra platform is adaptable, consistent across environments, and compliant with frameworks like GDPR, CCPA, and industry-specific regulations.
Use Case: Securing GenAI at Scale with Sentra
Consider a marketing platform using generative AI to create branded content for multiple enterprise clients—a common scenario facing organizations today.
Challenges:
- AI models processing proprietary brand data require robust enterprise data protection.
- Prompt injections could potentially leak confidential company messaging.
- Scalable security that doesn't impede creative workflows is a must.
Sentra’s data-first security approach tackles these issues head-on via:
- Data discovery & classification: Specialized AI models identify and safeguard sensitive information.

- Data access governance (DAG): The platform tracks who accesses training and RAG data, and when, establishing accountability and controlling permissions at a granular level. In addition, access to the AI agent (and its underlying information) is controlled and minimized.
- Real-time leakage detection: Sentra’s best-of-breed data labeling engine feeds internal DLP mechanisms that are part of the AI agents (as well as external 3rd-party DLP and DDR tools). In addition, Sentra monitors the interaction between the users and the AI agent, allowing for the detection of sensitive outputs, malicious inputs, or anomalous behavior.
- Scalable endpoint threat detection: The solution protects API interactions from adversarial attacks, securing both proprietary and third-party AI services.
- Automated security alerts: Sentra integrates with ServiceNow and Jira for rapid incident response, streamlining security operations.
The outcome: Sentra provides a scalable DSPM solution for AI that secures enterprise data while enabling AI-powered innovation, helping organizations address the complex challenges of enterprise AI adoption.
Takeaways
AI security starts at the data layer - without securing enterprise data, even the most sophisticated AI implementations remain vulnerable to attacks and data exposure. As organizations develop their data security strategies for AI, prioritizing data observability, governance, and protection creates the foundation for responsible innovation.
Sentra's DSPM provides cutting-edge AI security solutions at the scale required for enterprise adoption, helping organizations implement AI security best practices while maintaining compliance with evolving regulations.
Learn more about how Sentra has built a data security platform designed for the AI era.
<blogcta-big>