Understanding the FTC Data Breach Reporting Requirements
More Companies Need to Report Data Breaches
In a significant move towards enhancing data security and transparency, new data breach reporting rules have taken effect for various financial institutions. Since May 13, 2024, non-banking financial institutions, including mortgage brokers, payday lenders, and tax preparation firms, must report data breaches to the Federal Trade Commission (FTC) within 30 days of discovery. This new mandate, part of the FTC's Safeguards Rule, expands the breach notification requirements to a broader range of financial entities not overseen by the Securities and Exchange Commission (SEC).
Furthermore, by June 15, 2024, smaller reporting companies—those with a public float under $250 million or annual revenues under $100 million—must comply with the SEC’s new cybersecurity incident reporting rules, aligning their disclosure obligations with those of larger corporations. These changes mark a significant step towards enhancing transparency and accountability in data breach reporting across the financial sector.
How Can Financial Institutions Secure Their Data?
Understanding and tracking your sensitive data is fundamental to robust data security practices. The first step in safeguarding data is detecting and classifying what you have. It's far easier to protect data when you know it exists. This allows for appropriate measures such as encryption, controlling access, and monitoring for unauthorized use. By identifying and mapping your data, you can ensure that sensitive information is adequately protected and compliance requirements are met.
Identify Sensitive Data: Data is constantly moving, which makes it a challenge to know exactly what data you have and where it resides. This includes customer information, financial records, intellectual property, and any other data deemed sensitive. Having an automated data classification tool is a crucial first step. This includes ‘shadow’ data that may not be well known or well managed.
Data Mapping: Create and maintain an up-to-date map of your data landscape. This map should show where data is stored, processed, and transmitted, and who has access to it. It helps in quickly identifying which systems and data were affected by a breach and the impact blast radius (how extensive is the damage).
"Your Data Has Been Breached, Now What?"
When a data breach occurs, the immediate response is critical in mitigating damage and addressing the aftermath effectively. The investigation phase is particularly crucial as it determines the extent of the breach, the type and sensitivity of the data compromised, and the potential impact on the organization.
A key challenge during the investigation phase is understanding where the sensitive data was located at the time of the data breach and why or how existing controls were insufficient.
Without a proper data classification process or solution in place, it is difficult to ascertain the exact locations of the sensitive data or the applicable security posture at the time of the breach within the short timeframe required by the SEC and FTC reporting rules.
Here's a breakdown of the essential steps and considerations during the investigation phase:
1. Develop Appropriate Posture Policies and Enforce Adherence:
Establish policies that alert on and can help enforce appropriate security posture and access controls - these can be out-of-the-box fitting various compliance frameworks or can be customized for unique business or privacy requirements. Monitor for policy violations and initiate appropriate remediation actions (which can include ticket issuance, escalation notification, and automated access revocation or de-identification).
2. Conduct the Investigation: Determine Data Breach Source:
Identify how the breach occurred. This could involve phishing attacks, malware, insider threats, or vulnerabilities in your systems.
According to the FTC, it is critical to clearly describe what you know about the compromise. This includes:
- How it happened
- What information was taken
- How the thieves have used the information (if you know)
- What actions you have taken to remedy the situation
- What actions you are taking to protect individuals, such as offering free credit monitoring services
- How to reach the relevant contacts in your organization
Create a Comprehensive Plan: Additionally, create a comprehensive plan that reaches all affected audiences, such as employees, customers, investors, business partners, and other stakeholders.
Affected and Duplicated Data: Ascertain which data sets were accessed, altered, or exfiltrated. This involves checking logs, access records, and utilizing forensic tools. Assess if sensitive data has been duplicated or moved to unauthorized locations. This can compound the risk and potential damage if not addressed promptly.
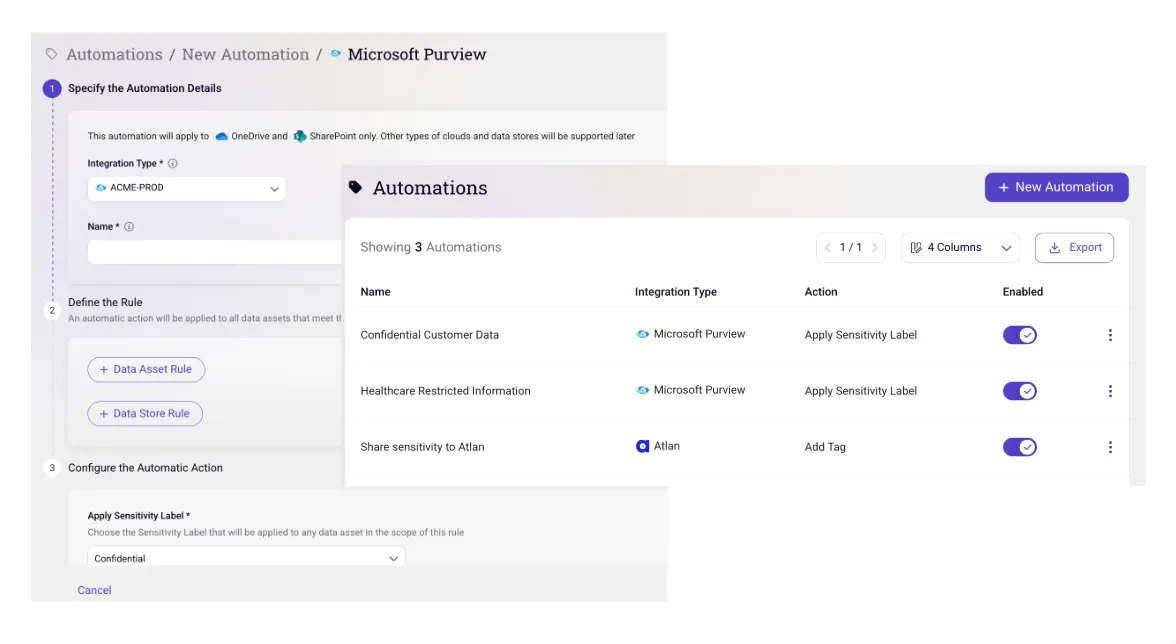
How Sentra Helps Automate Compliance and Incident Response
Sentra’s Data Security Posture Management solution provides organizations with full visibility into their data’s locations (including shadow data) and an up-to-date data catalog with classification of sensitive data. Sentra provides this without any complex deployment or operational work involved, this is achieved due to a cloud-native agentless architecture, using cloud provider APIs and mechanisms.
Below you can see the different data stores on the Sentra dashboard.

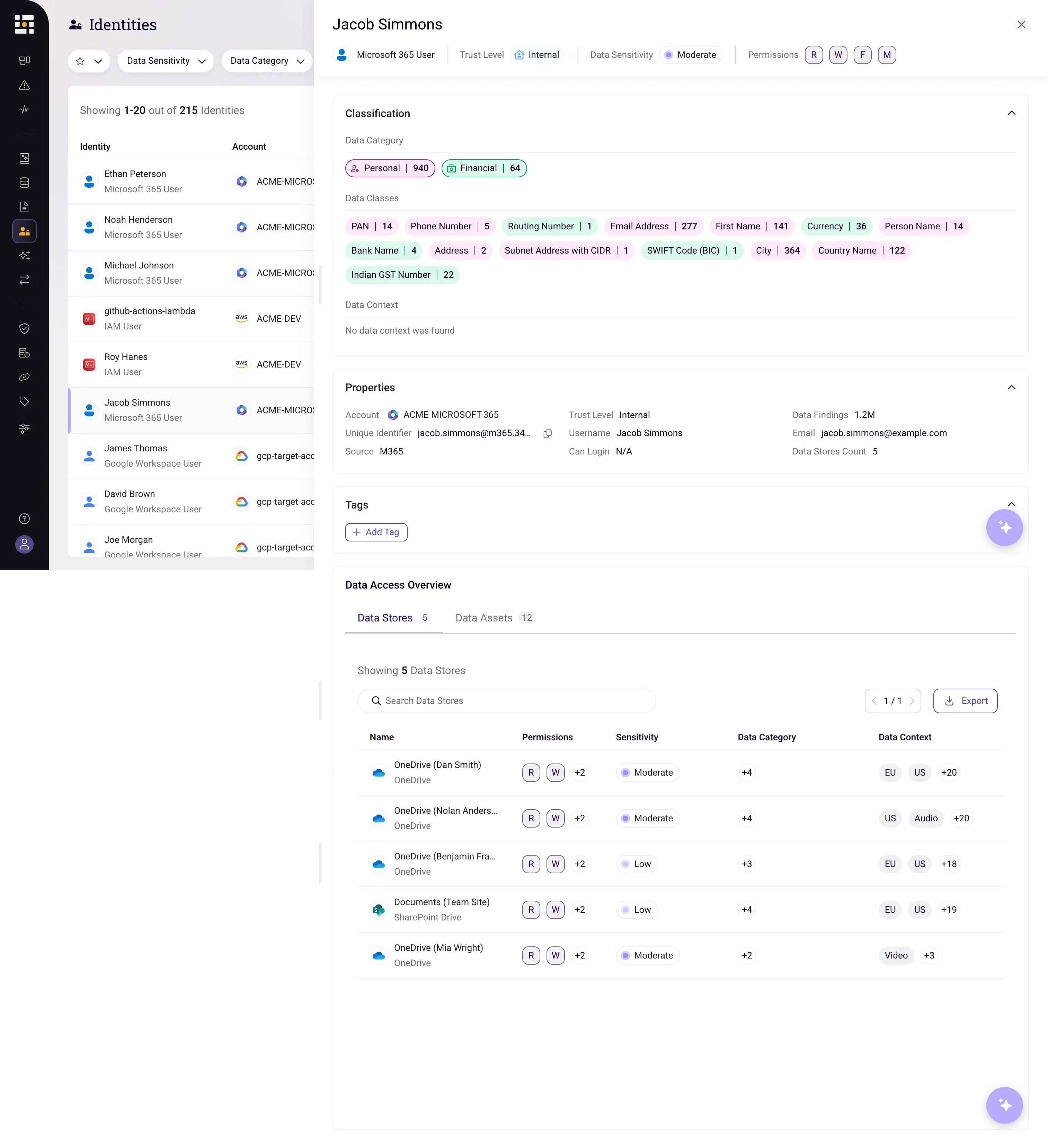
Sentra Makes Data Access Governance (DAG) Easy
Sentra helps you understand which users have access to what data and enrich metadata catalogs for comprehensive data governance. The accurate classification of cloud data provides advanced classification labels, including business context regarding the purpose of data, and automatic discovery, enabling organizations to gain deeper insights into their data landscape. This both enhances data governance while also providing a solid foundation for informed decision-making.
Sentra's detection capabilities can pinpoint over permissioning to sensitive data, prompting organizations to swiftly control them. This proactive measure not only mitigates the risk of potential breaches but also elevates the overall security posture of the organization by helping to institute least-privilege access.
Below you can see an example of a user’s access and privileges to which sensitive data.

Breach Reporting With Sentra
Having a proper classification solution helps you understand what kind of data you have at all times.
With Sentra, it's easier to pull the information for the report and understand whether there was sensitive data at the time of breach, what kind of data there was, and who/what had access to it, in order to have an accurate report.

To learn more about how you can gain full coverage and an up-to-date data catalog with classification of sensitive data, schedule a live demo with our experts.
<blogcta-big>









.webp)

.webp)
.webp)
