Securing Your Microsoft 365 Environment with Sentra
Picture this scenario: a senior employee at your organization has access to a restricted folder in SharePoint that contains sensitive data. Another employee needs access to a specific document in the folder and asks the senior employee for help. To save time, the senior employee simply copies the entire document and drops it into a folder with less stringent access controls so the other employee can easily access it. Because of this action taken by the senior employee, which only took seconds to complete, there’s now a copy of sensitive data — outside a secure folder and unknown to the data security team.
The Sentra team hears repeatedly that Microsoft 365 services, like SharePoint, are a pressing concern for data security teams because this type of data proliferation is so common. While Microsoft services like OneDrive, SharePoint, Office Online, and Teams drive productivity and collaboration, they also pose a unique challenge for data security teams: identifying and securing the constantly changing data landscape without inhibiting collaboration or slowing down innovation.
Today’s hybrid environments — including Microsoft 365 services — present many new security challenges. Teams must deal with vast and dynamic data within SharePoint, coupled with explosive cloud growth and data movement between environments (cloud to on prem or vice versa). They must also find ways to find and secure the unstructured sensitive data stored within Microsoft 365 services.
Legacy, connector- and agent-based solutions can’t fit the bill — they face performance and scaling constraints and are an administrative nightmare for teams trying to keep pace. Instead, teams need a data security solution that can automatically comprehend unstructured data in several formats and is more responsive and reliable than legacy tools.
A cloud-native approach is one viable, scalable solution to address the multitude of security challenges that complex, modern environments create. It provides versatile, agile protection for the multi-cloud, hybrid, SaaS (i.e., Microsoft), and on-prem environments that comprise a business’s operations.
The Challenge of Protecting Your Microsoft 365 Environment
When employees use Microsoft 365, they can copy, move, or delete data instantly, making it challenging to keep track of where sensitive data resides and who has access to it. For instance, sensitive data can easily be stored improperly or left behind in a OneDrive after an employee leaves an organization. This is commonplace when using Teams and/or SharePoint for document collaborations. This misplaced sensitive data can become ammunition for an insider threat, such as a disgruntled employee who wants to cause company damage.

Defending your Microsoft 365 environment against these risks can be difficult because Microsoft 365 stores data, such as Teams messages or OneDrive documents, in a free-form layout. It’s far more challenging to classify this unstructured data than it is to classify structured data because it doesn’t follow a clear schema and formatting protocol. For instance, in a structured database, sensitive information like names and birthdates would be stored in neighboring columns labeled “names” and “birthdates.” However, in an unstructured data environment like Microsoft 365, someone might share their birthdate or other PII in a quick Teams message to an HR staff member, which is then stored in SharePoint behind the scenes.
In addition, unstructured data lacks context. Some data is only considered sensitive under certain conditions. For example, 9-digit passport numbers alone wouldn’t pose a significant risk if exposed, while a combination of passport numbers and the identity of the passport holders would. Structured databases make it easy to see these relationships, as they likely contain column titles (e.g., “passport number,” “passport holder name”) or other clear schemas. Unstructured file repositories, on the other hand, might have all of this information buried in documents with a free-form block of text, making it especially difficult for teams to understand the context of each data asset fully.
Protection Measures to Address Microsoft 365 Data Risks
Today’s businesses must get ahead of these challenges by instituting best practices such as least privilege access, or else face consequences such as violating compliance regulations or putting sensitive data at risk of exposure.
Since sensitive data is far more nuanced and complex to discern in Microsoft 365, businesses need a cloud-native solution that identifies the subtle signs associated with sensitive data in unstructured cloud environments and takes appropriate action to protect it.
Sentra’s Integration with Microsoft 365
Sentra’s data security posture management (DSPM) platform enables secure collaboration and file sharing across services such as SharePoint, OneDrive, Teams, OneNote, and Office Online.
Its new integration with Microsoft 365 offers unmatched discovery and classification capabilities for security, data owners and risk management teams to secure data — not stopping activity but allowing it to happen securely. Here are a few of the features we offer teams using Microsoft 365:
Advanced ML/AI analysis for accurate data discovery.
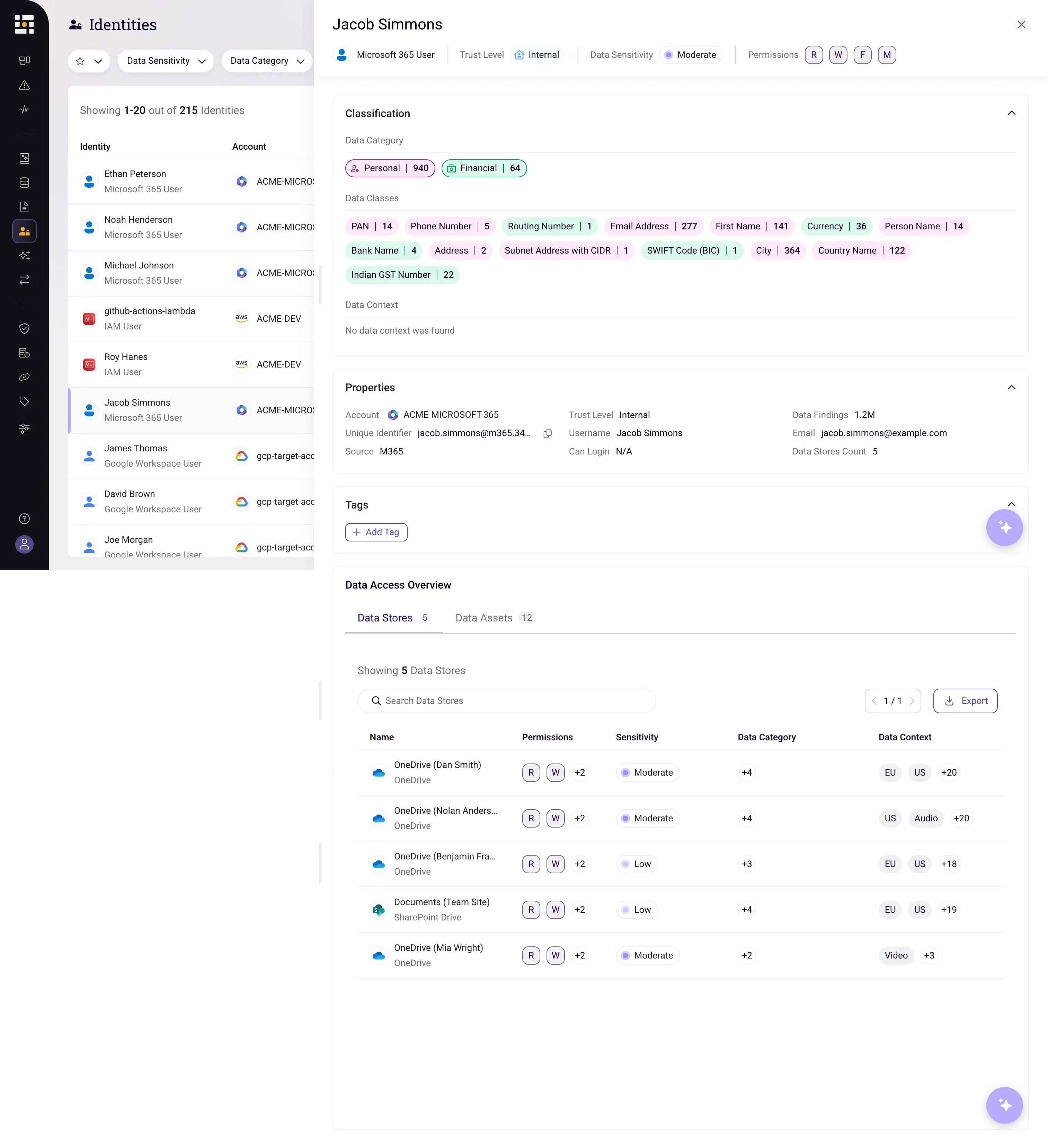
Sentra’s data security platform can autonomously discover data across your entire environment, including shadow data (i.e., misplaced, abandoned, or unknown data) or migrated data (data that may have sprawled to a lesser protected environment). It can then accurately rank data sensitivity levels by conducting in-depth analysis based on nuanced contextual information such as metadata, location, neighboring assets, and file path.

This contextual approach differs from traditional security methods, which rely on very prescriptive data formats and overlook unstructured data that doesn’t fit into these formats. Sentra’s high level of accuracy minimizes the number of false positives, requiring less hands-on validation from your team.
Use case scenario: An employee has set up their company OneDrive account to be directly accessible through their personal computer’s central file system. While working on personal tasks on their computer, this employee accidentally saves their child’s medical paperwork inside the company OneDrive rather than a personal file. To prevent this situation, Sentra can discover and notify the appropriate users if PII is residing in a OneDrive business account and violating company policy.
Precise data classification to support remediation.
After discovering sensitive data, Sentra classifies the data using data context classes. This granular classification level provides rich usage context and enables teams to perform better risk prioritization, sensitivity analysis, and control actioning. Its data context classes can identify very specific types of data: configuration, log, tabular, image, etc. By labeling their resources with this level of precision and context, businesses can better understand usage and which files are more likely to contain sensitive information and which are not.
In addition, Sentra consolidates classified data security findings from across your entire data estate into a single platform. This includes insights from multiple cloud environments, SaaS platforms, and on-premises data stores. Sentra offers a centralized, always-up-to-date data catalog and visualizations of data movement between environments.
Use case scenario: An employee requests access to a SharePoint folder containing a nonsensitive document. A senior employee authorizes access without realizing that sensitive documents are also stored within this folder. To prevent this type of excessive privileged access, Sentra labels sensitive documents, emails, and other Microsoft file formats so your team can enforce access policies and take the correct actions to secure these assets.
Guardrails to enforce data hygiene across your environment.
Sentra also enforces data hygiene best practices across your Microsoft 365. environment, proactively preventing staff from taking risky actions or going against company policies.
For instance, it can determine excessive access permission and alert on these violations. Sentra can also monitor sharing permissions to enforce least privilege access on sensitive files.
Use case scenario: During onboarding, a new junior employee is given access permissions across Microsoft 365 services. By default, they now have access to confidential intellectual property stored in SharePoint, even though they’ll never need this information in their daily work. To prevent this type of excessive access control, Sentra can enforce more stringent access controls for sensitive SharePoint folders.
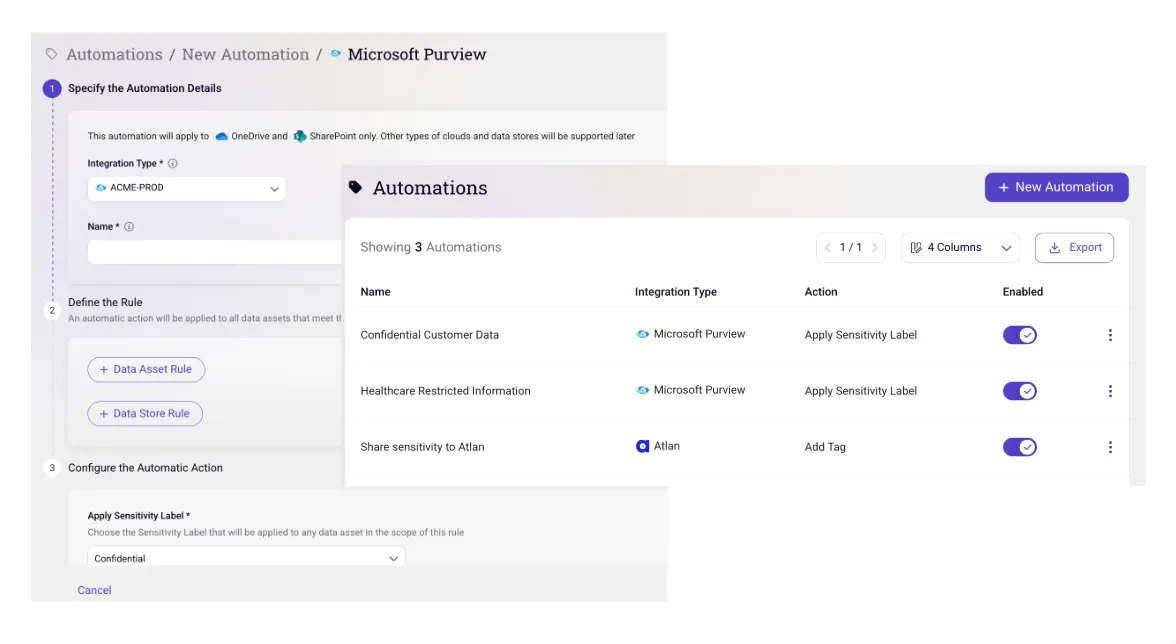
Automation to accelerate incident response.
Sentra also supports automated incident response with early breach detections. It can identify data similarities to instigate an investigation of potentially risky data proliferation. In addition, it provides real-time alerting when any anomalous activity occurs within the environment and supports incident investigation and breach impact analysis with automated remediation and in-product guidance. Sentra also integrates with data catalogs and other incident response/ITSM tools to quickly alert the proper teams and kick off the right response processes.
Use case example: An employee who was just laid off feels disgruntled with the company. They decide to go into SharePoint and start a large download of several files containing intellectual property. To protect your data from these types of internal threats, Sentra can immediately detect and alert you to suspicious activities, such as unusual activity, within your Microsoft 365 environment.
DSPM, the Key to Securing Microsoft 365
After talking with many customers and prospects facing challenges securing Microsoft 365, the Sentra team has seen the significance of a DSPM platform compatible with services like SharePoint, OneDrive, and Office Online. We prioritize bringing all data, including assets buried in your Microsoft 365 environment, into view so you can better safeguard it without slowing down innovation and collaboration.
Dive deeper into the world of Data Security Posture Management (DSPM) and discover how it helps organizations secure their entire data estate, including cloud, on-prem, and SaaS data stores (like Microsoft 365).
To learn more about Sentra's DSPM, and how you can secure your entire data estate, please visit Sentra's demo page.
<blogcta-big>









.webp)

.webp)
.webp)
