The Importance of Data Security for Growth: A Blueprint for Innovation
“For whosoever commands the sea commands the trade; whosoever commands the trade of the world commands the riches of the world, and consequently the world itself.” — Sir Walter Raleigh.
For centuries, power belonged to those who ruled the seas. Today, power belongs to those who control and harness their data’s potential. But let’s face it—many organizations are adrift, overwhelmed by the sheer volume of data and rushing to keep pace in a rapidly shifting threatscape. Navigating these waters requires clarity, foresight, and the right tools to stay afloat and steer toward success. Sound familiar?
In this new reality, controlling data now drives success. But success isn’t just about collecting data, it’s about being truly data-driven. For modern businesses, data isn’t just another resource. Data is the engine of growth, innovation, and smarter decision-making.
Yet many leaders still grapple with critical questions:
- Are you really in control of your data?
- Do you make decisions based on the insights your data provides?
- Are you using it to navigate toward long-term success?
In this blog, I’ll explore why mastering your data isn’t just a strategic advantage—it’s the foundation of survival in today’s competitive market - Data is the way to success and prosperity in an organization. I’ll also break down how forward-thinking organizations are using comprehensive Data Security Platforms to navigate this new era where speed, innovation, and security can finally coexist.
The Role of Data in Organizational Success
Data drives innovation, fuels growth, and powers smart decision-making. Businesses use data to develop new products, improve customer experiences, and maintain a competitive edge. But let’s be clear, collecting vast amounts of data isn’t enough. True success comes from securing it, understanding it, and putting it to work effectively.
If you don’t fully understand or protect your data, how valuable can it really be?
Organizations face a constant barrage of threats: data breaches, shadow data, and excessive access permissions. Without strong safeguards, these vulnerabilities don’t just pose risks—they become ticking time bombs.
For years, controlling and understanding your data was impossible—it was a complex, imprecise, expensive, and time-consuming process that required significant resources. Today, for the first time ever, there is a solution. With innovative approaches and cutting-edge technology, organizations can now gain the clarity and control they need to manage their data effectively!
With the right approach, businesses can transform their data management from a reactive process to a competitive advantage, driving both innovation and resilience. As data security demands grow, these tools have evolved into something much more powerful: comprehensive Data Security Platforms (DSPs). Unlike basic solutions, you can expect a data security platform to deliver advanced capabilities such as enhanced access control, real-time threat monitoring, and holistic data management. This all-encompassing approach doesn’t just protect sensitive data—it makes it actionable and valuable, empowering organizations to thrive in an ever-changing landscape.
Building a strong data security strategy starts with visionary leadership. It’s about creating a foundation that not only protects data but enables organizations to innovate fearlessly in the face of uncertainty.
The Three Key Pillars for Securing and Leveraging Data
1. Understand Your Data
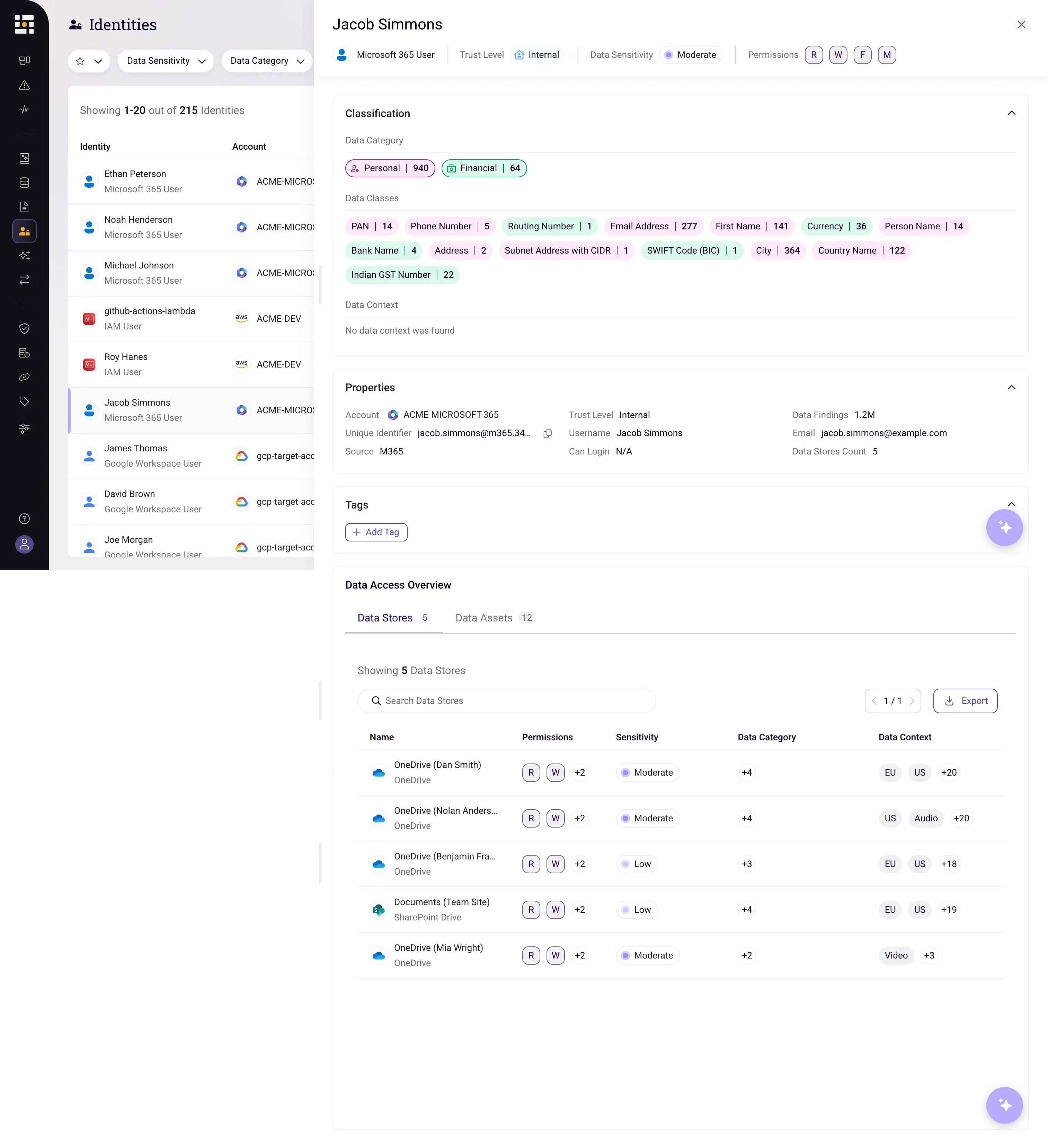
The foundation of any data security strategy is visibility. Knowing where your data is stored, who has access to it, and what sensitive information it contains is essential. Data sprawl remains a challenge for many organizations. The latest tools, powered by automation and intelligence, provide unprecedented clarity by discovering, classifying, and mapping sensitive data. These insights allow businesses to make sharper, faster decisions to protect and harness their most valuable resource.
Beyond discovery, advanced tools continuously monitor data flows, track changes, and alert teams to potential risks in real-time. With a complete understanding of their data, organizations can shift from reactive responses to proactive management.
2. Control Your Data
Visibility is the first step; control is the next. Managing access to sensitive information is critical to minimizing risk. This involves identifying overly broad permissions and ensuring that access is granted only to those who truly need it.
Having full control of your data becomes even more challenging when data is copied or moved between environments—such as from private to public or from encrypted to unencrypted. This process creates "similar data," in which data that was initially secure becomes exposed to greater risk by being moved into a lower environment. Data that was once limited to a small, regulated group of identities (users) then becomes accessible by a larger number of users, resulting in a significant loss of control.
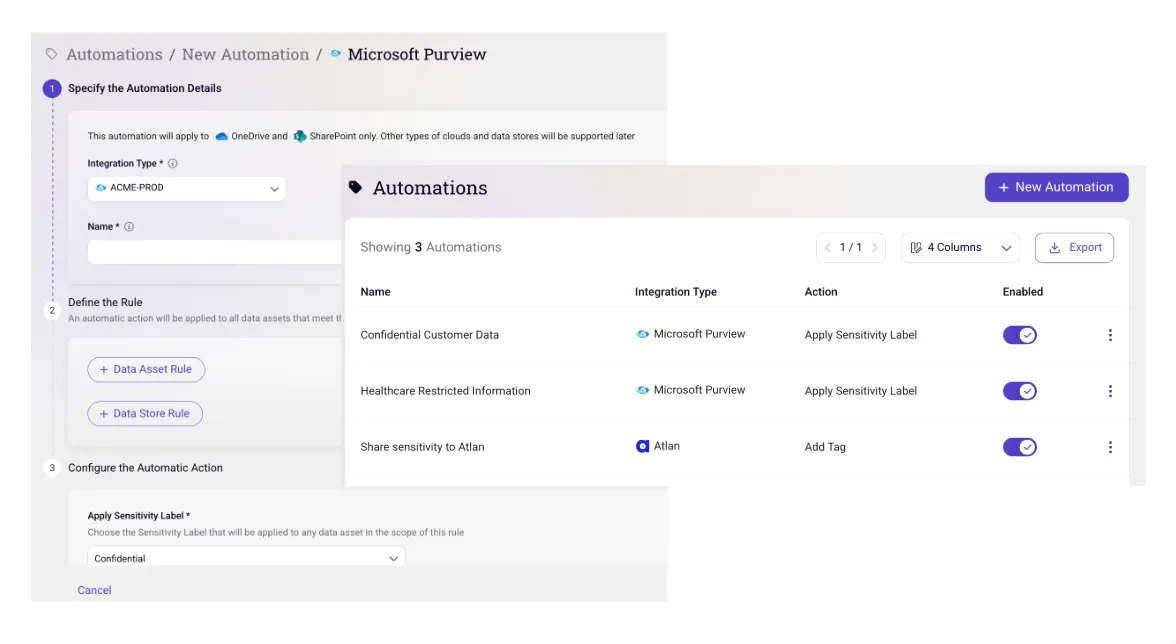
Effective data security strategies go beyond identifying these issues. They enforce access policies, automate corrective actions, and integrate with identity and access management systems to help organizations maintain a strong security posture, even as their business needs change and evolve. In addition to having robust data identification methods, it’s crucial to prioritize the implementation of access control measures. This involves establishing Role-based Access Control (RBAC) and Attribute-based Access Control (ABAC) policies, so that the right users have permissions at the right times.
3. Monitor Your Data
Real security goes beyond awareness—it demands a dynamic approach. Real-time monitoring doesn’t just detect risks and threats; it anticipates them. By spotting unusual behaviors or unauthorized access early, businesses can preempt incidents and maintain trust in an increasingly volatile digital environment. Advanced tools provide visibility into suspicious activities, offer real-time alerts, and automate responses, enabling security teams to act swiftly. This ongoing oversight ensures that businesses stay resilient and adaptive in an ever-changing environment.
Being Fast and Secure
In today’s competitive market, speed drives success—but speed without security is a recipe for disaster. Organizations must balance rapid innovation with robust protection.
Modern tools streamline security operations by delivering actionable insights for faster, more informed risk responses. A comprehensive Data Security Platform goes further by integrating security workflows, automating threat detection, and enabling real-time remediation across multi-cloud environments. By embedding security into daily processes, businesses can maintain agility while protecting their most critical assets.
Why Continuous Data Security is the Key to Long-Term Growth
Data security isn’t a one-and-done effort—it’s an ongoing commitment. As businesses scale and adopt new technologies, their data environments grow more complex, and security threats continue to evolve. Organizations that continuously understand and control their data are poised to turn uncertainty into opportunity. By maintaining this control, they sustain growth, protect trust, and future-proof their success.
Adaptability is the foundation of long-term success. A robust data security platform evolves with your business, providing continuous visibility, automating risk management, and enabling proactive security measures. By embedding these capabilities into daily operations, organizations can maintain speed and agility without compromising protection.
In today’s data-driven world, success hinges on making informed decisions with secure data. Businesses that master continuous data security will not only safeguard their assets but also position themselves to thrive in an ever-changing competitive landscape.
Conclusion: The Critical Link Between Data Security and Success
Data is the lifeblood of modern businesses, driving growth, innovation, and decision-making. But with this immense value comes an equally immense responsibility: protecting it. A comprehensive data security platform goes beyond the basics, unifying discovery, classification, access governance, and real-time protection into a single proactive approach. True success in a data-driven world demands more than agility—it requires mastery. Organizations that embrace data security as a catalyst for innovation and resilience are the ones who will lead the way in today’s competitive landscape.
The question is: Will you lead the charge or risk being left behind? The opportunity to secure your future starts now.
Final thought: In my work with organizations across industries, I’ve seen firsthand how those who treat data security as a strategic enabler, rather than an obligation, consistently outperform their peers. The future belongs to those who lead with confidence, clarity, and control.
If you're interested in learning how Sentra's Data Security Platform can help you understand and protect your data to drive success in today’s competitive landscape, request a demo today.
<blogcta-big>









.webp)

.webp)
.webp)
