Building Automated Data Security Policies for 2026: What Security Teams Need Now
Learn how to build automated data security policies that reduce data exposure, meet GDPR, PCI DSS, and HIPAA requirements, and scale data governance across cloud, SaaS, and AI-driven environments as organizations move into 2026.
As 2025 comes to a close, one reality is clear: automated data security and governance programs are a must-have to truly leverage data and AI. Sensitive data now moves faster than human review can keep up with. It flows across multi-cloud storage, SaaS platforms, collaboration tools, logging pipelines, backups, and increasingly, AI and analytics workflows that continuously replicate data into new locations. For security and compliance teams heading into 2026, periodic audits and static policies are no longer sufficient. Regulators, customers, and boards now expect continuous visibility and enforcement.
This is why automated data security policies have become a foundational control, not a “nice to have.”
In this blog, we focus on how data security policies are actually used at the end of 2025, and how to design them so they remain effective in 2026.
You’ll learn:
- The most important compliance and risk-driven policy use cases
- How organizations operationalize data security policies at scale
- Practical examples aligned with GDPR, PCI DSS, HIPAA, and internal governance
Why Automated Data Security Policies Matter Heading into 2026
The direction of regulatory enforcement and threat activity is consistent:
- Continuous compliance is now expected, not implied
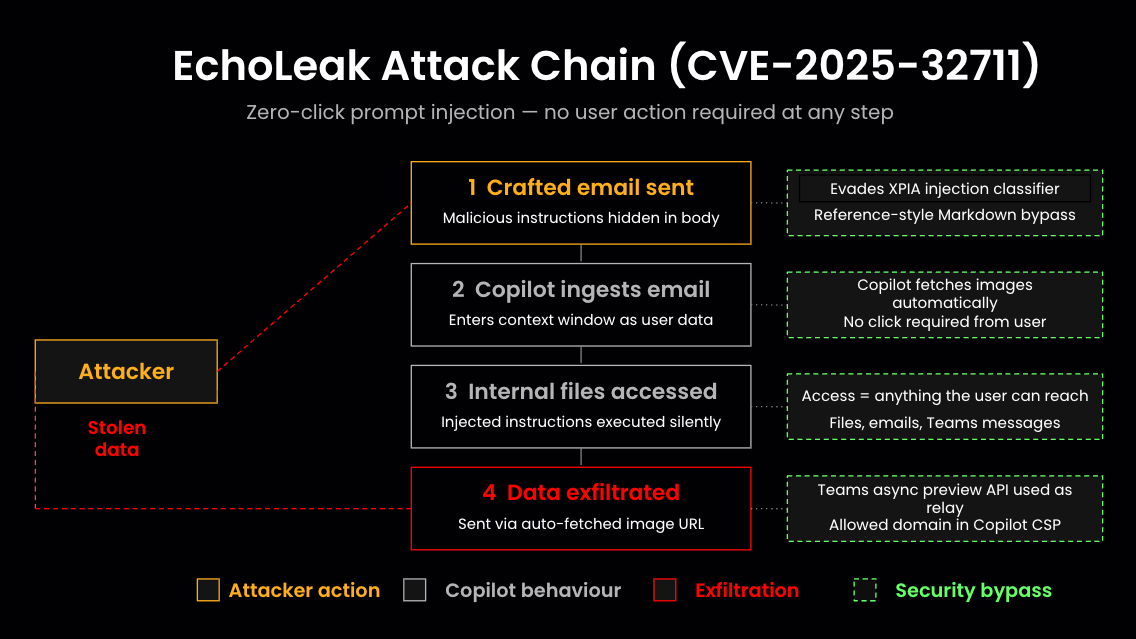
- Overexposed data is increasingly used for extortion, not just theft
- Organizations must prove they know where sensitive data lives and who can access it
Recent enforcement actions have shown that organizations can face penalties even without a breach, simply for storing regulated data in unapproved locations or failing to enforce access controls consistently.
Automated data security policies address this gap by continuously evaluating:
- Data sensitivity
- Access scope
- Storage location and residency
- surfacing violations in near real time.
Three Data Security Policy Use Cases That Deliver Immediate Value
As organizations prepare for 2026, most start with policies that reduce data exposure quickly.
1. Limiting Data Exposure and Ransomware Impact
Misconfigured access and excessive sharing remain the most common causes of data exposure. In cloud and SaaS environments, these issues often emerge gradually, and go unnoticed without automation.
High-impact policies include:
- Sensitive data shared with external users: Detect files containing credentials, PII, or financial data that are accessible to outside collaborators.
- Overly broad internal access to sensitive data: Identify data shared with “Anyone in the organization,” significantly increasing exposure during account compromise.
These policies reduce blast radius and help prevent data from becoming leverage in extortion-based attacks.
2. Enforcing Secure Data Storage and Handling (PCI DSS, HIPAA, SOC 2)
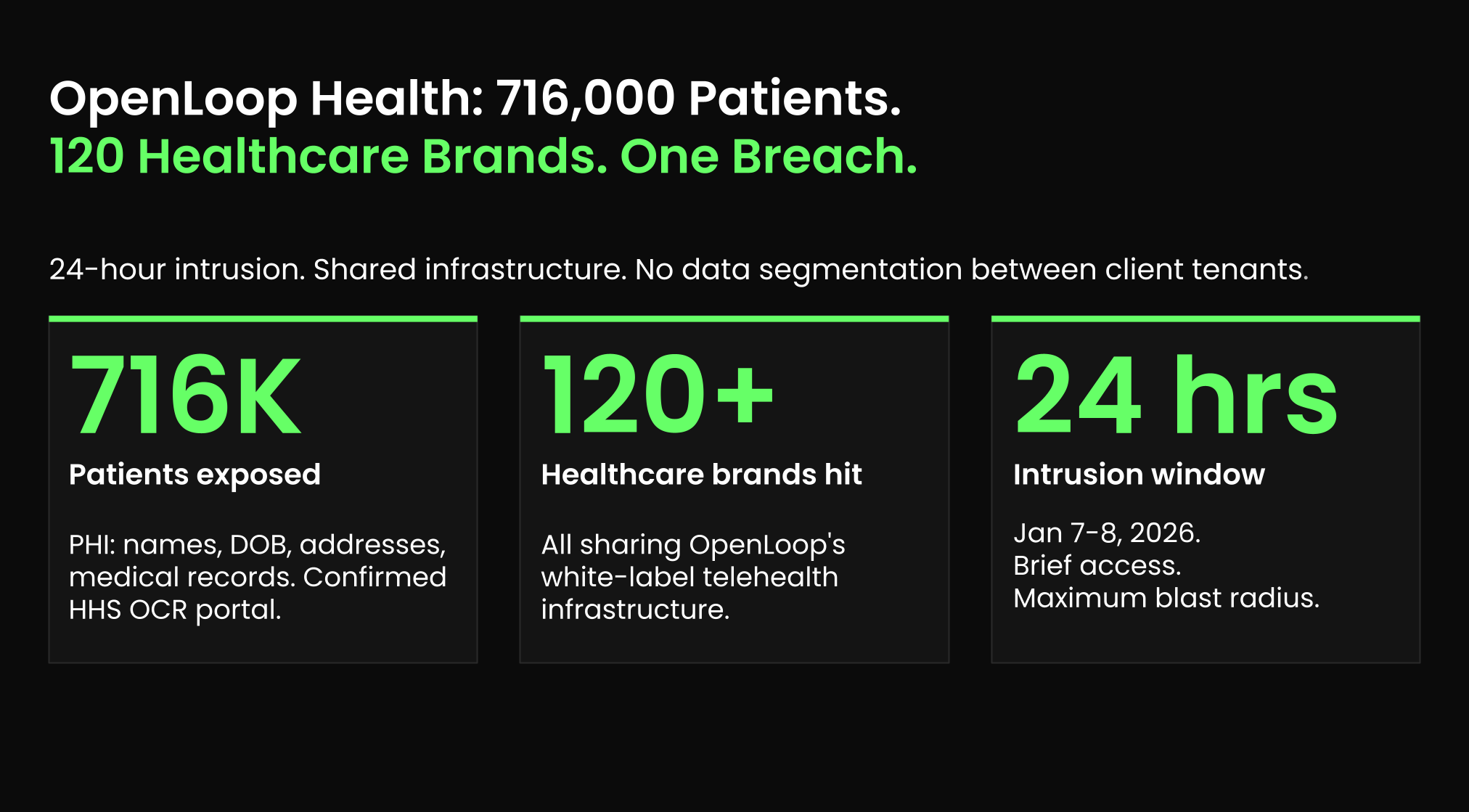
Compliance violations in 2025 rarely result from intentional misuse. They happen because sensitive data quietly appears in the wrong systems.
Common policy findings include:
- Payment card data in application logs or monitoring tools: A persistent PCI DSS issue, especially in modern microservice environments.
- Employee or patient records stored in collaboration platforms: PII and PHI often end up in user-managed drives without appropriate safeguards.
Automated policies continuously detect these conditions and support fast remediation, reducing audit findings and operational risk.
3. Maintaining Data Residency and Sovereignty Compliance
As global data protection enforcement intensifies, data residency violations remain one of the most common and costly compliance failures.
Automated policies help identify:
- EU personal data stored outside approved EU regions: A direct GDPR violation that is common in multi-cloud and SaaS environments.
- Cross-region replicas and backups containing regulated data: Secondary storage locations frequently fall outside compliance controls.
These policies enable organizations to demonstrate ongoing compliance, not just point-in-time alignment.
What Modern Data Security Policies Must Do (2026-Ready)
As teams move into 2026, effective data security policies share three traits:
- They are data-aware: Policies are based on data sensitivity - not just resource labels or storage locations.
- They operate continuously: Policies evaluate changes as data is created, moved, shared, or copied into new systems.
- They drive action: Every violation maps to a remediation path: restrict access, move data, or delete it.
This is what allows security teams to scale governance without slowing the business.
Conclusion: From Static Rules to Continuous Data Governance
Heading into 2026, automated data security policies are no longer just compliance tooling, they are a core layer of modern security architecture.
They allow organizations to:
- Reduce exposure and ransomware risk
- Enforce regulatory requirements continuously
- Govern sensitive data across cloud, SaaS, and AI workflows
Most importantly, they replace reactive audits with real-time data governance.
Organizations that invest in automated, data-aware security policies today will enter 2026 better prepared for regulatory scrutiny, evolving threats, and the continued growth of their data footprint.
<blogcta-big>