Meni Besso
Meni is an experienced product manager and the former founder of Pixibots (A mobile applications studio). In the past 15 years, he gained expertise in various industries such as: e-commerce, cloud management, dev-tools, mobile games, and more. He is passionate about delivering high quality technical products, that are intuitive and easy to use.
Name's Data Security Posts

Automating Records of Processing Activities (ROPA) with Real Data Visibility
Automating Records of Processing Activities (ROPA) with Real Data Visibility
Enterprises managing sprawling multi-cloud environments struggle to keep ROPA (Records of Processing Activities) reporting accurate and up to date for GDPR compliance. As manual, spreadsheet-based workflows hit their limits, automation has become essential - not just to save time, but to build confidence in what data is actually being processed across the organization.
Recently, during a strategy session, a leading GDPR-regulated customer shared how they are using Sentra to move beyond manual ROPA processes. By relying on Sentra’s automated data discovery, AI-driven classification, and environment-aware reporting, the organization has operationalized a high-confidence ROPA across ~100 cloud accounts. Their experience highlights a critical shift: ROPA as a trusted source of truth rather than a checkbox exercise.
Why ROPA Often Comes Up Short in Practice
For many organizations, maintaining a ROPA is a regulatory requirement, but not a reliable one.
As the customer explained:
“What I’ve often seen is the ROPA or the records of processing activity being something that is a very checkbox thing to do. And that’s because it’s really hard to understand what data you actually have unless you literally go and interrogate every database.”
Without direct visibility into cloud data stores, ROPA documentation often relies on assumptions, interviews, and outdated spreadsheets. This approach doesn’t scale and creates risk during audits, due diligence, and regulatory inquiries, especially for companies operating across multiple clouds or growing through acquisition.
From Guesswork to a High-Confidence ROPA
The same customer described how Sentra fundamentally changed their approach:
“What Sentra allowed us to do is really have what I’ll describe as a high confidence ROPA. Our ROPA wasn’t guesswork, it was based on actual information that Sentra had gone out, touched our databases, looked inside them, identified the specific types of data records, and then gave us that inventory of what we had.”
By directly scanning databases and cloud data stores, Sentra replaces assumptions with facts. ROPA reports are generated from live discovery results, giving compliance teams confidence that they can accurately attest to:
- What personal data they hold
- Where it resides
- How it is processed
- And how it is governed
This transforms ROPA from a static document into a defensible, audit-ready asset.
The Need for Automated ROPA Reporting at Scale
Manual ROPA reporting becomes unmanageable as cloud environments expand. Organizations with dozens or hundreds of cloud accounts quickly face gaps, inconsistencies, and outdated records. Industry research shows that privacy automation can reduce manual ROPA effort by up to 80% and overall compliance workload by 60%. But effective automation requires focus. Reporting must concentrate on production environments, where real customer data lives, rather than drowning teams in noise from test or development systems.
As a privacy champion on this project, explains:
“What I’m interested in is building a data inventory that gives me insight from a privacy point of view on what kind of customer data we are holding.”
This shift toward privacy-focused inventories ensures ROPA reporting stays meaningful, actionable, and aligned with regulatory intent.
How Sentra Enables Template-Driven, Environment-Aware ROPA Reporting
Sentra’s reporting framework allows organizations to create custom ROPA templates tailored to their regulatory, operational, and business needs. These templates automatically pull from continuously updated discovery and classification results, ensuring reports stay accurate as environments evolve.
A critical component of this approach is environment tagging. By clearly distinguishing production systems from non-production environments, Sentra ensures ROPA reports reflect only systems that actually process personal data. This reduces reporting noise, improves audit clarity, and aligns with modern GDPR automation best practices.
The result is ROPA reporting that is both scalable and precise - without requiring manual filtering or spreadsheet maintenance.
Solving the Data Classification Problem with Context-Aware AI
Accurate ROPA automation depends on intelligent data classification. Many tools rely on basic pattern matching, which often leads to false positives, such as mistaking airline or airport codes for regulated personal data in HR or internal systems.
Sentra addresses this challenge with AI-based, context-aware classification that understands how data is structured, where it appears, and how it is used. Rather than flagging data solely based on patterns, Sentra analyzes context to reliably distinguish between regulated personal data and non-regulated business data.
This approach dramatically reduces false positives and gives privacy teams confidence that ROPA reports reflect real regulatory exposure - without manual cleanup, lookup tables, or ongoing tuning.
What Sets Sentra Apart for ROPA Automation
While many platforms claim to support ROPA automation, few can deliver accurate, production-ready reporting across complex cloud environments. Sentra stands out through:
- Agentless data discovery
- Native multi-cloud support (AWS, Azure, GCP, and hybrid)
- Context-aware AI classification
- Data-centric inventory of all customer regulated data
- Flexible, customizable ROPA reporting templates
- Strong handling of inconsistent metadata and environment tagging
As the customer summarized:
“It’s no longer a checkbox exercise. It’s a very high confidence attestation of what we definitely have. That visibility allowed us to comply with GDPR in a much more comprehensive way.”
Conclusion
ROPA automation is not just about efficiency, it’s about trust. By grounding ROPA reporting in real data discovery, environment awareness, and AI-driven classification, Sentra enables organizations to replace guesswork with confidence.
The result is a scalable, defensible ROPA that reduces manual effort, lowers compliance risk, and supports long-term privacy maturity.
Interested in seeing high-confidence ROPA automation in action? Book a demo with Sentra to learn how you can turn ROPA into a living source of truth for GDPR compliance.
<blogcta-big>

How to Scale DSAR Compliance (Without Breaking Your Team)
How to Scale DSAR Compliance (Without Breaking Your Team)
Data Subject Access Requests (DSARs) are one of the most demanding requirements under privacy regulations such as GDPR and CPRA. As personal data spreads across cloud, SaaS, and legacy systems, responding to DSARs manually becomes slow, costly, and error-prone. This article explores why DSARs are so difficult to scale, the key challenges organizations face, and how DSAR automation enables faster, more reliable compliance.
Privacy regulations are no longer just legal checkboxes, they are a foundation of customer trust. In today’s data-driven world, individuals expect transparency into how their personal information is collected, used, and protected. Organizations that take privacy seriously demonstrate respect for their users, strengthening trust, loyalty, and long-term engagement.
Among these requirements, DSARs are often the most complex to support. They give individuals the right to request access to their personal data, typically with a strict response deadline of 30 days. For large enterprises with data scattered across cloud, SaaS, and on-prem environments, even a single request can trigger a frantic search across multiple systems, manual reviews, and legal oversight - quickly turning DSAR compliance into a race against the clock, with reputation and regulatory risk on the line.
What Is a Data Subject Access Request (DSAR)?
A Data Subject Access Request (DSAR) is a legal right granted under privacy regulations such as GDPR and CPRA that allows individuals to request access to the personal data an organization holds about them. In many cases, individuals can also request information about how that data is used, shared, or deleted.
Organizations are typically required to respond to DSARs within a strict timeframe, often 30 days, and must provide a complete and accurate view of the individual’s personal data. This includes data stored in databases, files, logs, SaaS platforms, and other systems across the organization.
Why DSAR Requests Are Difficult to Manage at Scale
DSARs are relatively manageable for small organizations with limited systems. At enterprise scale, however, they become significantly more complex. Personal data is no longer centralized. It is distributed across cloud platforms, SaaS applications, data lakes, file systems, and legacy infrastructure. Privacy teams must coordinate with IT, security, legal, and data owners to locate, review, and validate data before responding. As DSAR volumes increase, manual processes quickly break down, increasing the risk of delays, incomplete responses, and regulatory exposure.
Key Challenges in Responding to DSARs
Data Discovery & Inventory
For large organizations, pinpointing where personal data resides across a diverse ecosystem of information systems, including databases, SaaS applications, data lakes, and legacy environments, is a complex challenge. The presence of fragmented IT infrastructure and third-party platforms often leads to limited visibility, which not only slows down the DSAR response process but also increases the likelihood of missing or overlooking critical personal data.
Linking Identities Across Systems
A single individual may appear in multiple systems under different identifiers, especially if systems have been acquired or integrated over time. Accurately correlating these identities to compile a complete DSAR response requires sophisticated identity resolution and often manual effort.
Unstructured Data Handling
Unlike structured databases, where data is organized into labeled fields and can be efficiently queried, unstructured data (like PDFs, documents, and logs) is free-form and lacks consistent formatting. This makes it much harder to search, classify, or extract relevant personal information.
Response Timeliness
Regulatory deadlines force organizations to respond quickly, even when data must be gathered from multiple sources and reviewed by legal teams. Manual processes can lead to delays, risking non-compliance and fines.
Volume & Scalability
While most organizations can handle an occasional DSAR manually, spikes in request volume - driven by events like regulatory campaigns or publicized incidents - can overwhelm privacy and legal teams. Without scalable automation, organizations face mounting operational costs, missed deadlines, and an increased risk of inconsistent or incomplete responses.
The Role of Data Security Platforms in DSAR Automation
Sentra is a modern data security platform dedicated to helping organizations gain complete visibility and control over their sensitive data. By continuously scanning and classifying data across all environments (including cloud, SaaS, and on-premises systems) Sentra maintains an always up-to-date data map, giving organizations a clear understanding of where sensitive data resides, how it flows, and who has access to it. This data map forms the foundation for efficient DSAR automation, enabling Sentra’s DSAR module to search for user identifiers only in locations where relevant data actually exists - ensuring high accuracy, completeness, and fast response times.
.webp)
Another key factor in managing DSAR requests is ensuring that sensitive customer PII doesn’t end up in unauthorized or unintended environments. When data is copied between systems or environments, it’s essential to apply tokenization or masking to prevent unintentional sprawl of PII. Sentra helps identify misplaced or duplicated sensitive data and alerts when it isn’t properly protected. This allows organizations to focus DSAR processing within authorized operational environments, significantly reducing both risk and response time.
Smart Search of Individual Data
To initiate the generation of a Data Subject Access Request (DSAR) report, users can submit one or more unique identifiers—such as email addresses, Social Security numbers, usernames, or other personal identifiers—corresponding to the individual in question. Sentra then performs a targeted scan across the organization’s data ecosystem, focusing on data stores known to contain personally identifiable information (PII). This includes production databases, data lakes, cloud storage services, file servers, and both structured and unstructured data sources.
Leveraging its advanced classification and correlation capabilities, Sentra identifies all relevant records associated with the provided identifiers. Once the scan is complete, it compiles a comprehensive DSAR report that consolidates all discovered personal data linked to the data subject that can be downloaded as a PDF for manual review or securely retrieved via Sentra’s API.
.webp)
Establishing a DSAR Processing Pipeline
Large organizations that receive a high volume of DSAR (Data Subject Access Request) submissions typically implement a robust, end-to-end DSAR processing pipeline. This pipeline is often initiated through a self-service privacy portal, allowing individuals to easily submit requests for access or deletion of their personal data. Once a request is received, an automated or semi-automated workflow is triggered to handle the request efficiently and in compliance with regulatory timelines.
- Requester Identity Verification: Confirm the identity of the data subject to prevent unauthorized access (e.g., via email confirmation or secure login).
- Mapping Identifiers: Collect and map all known identifiers for the individual across systems (e.g., email, user ID, customer number).
- Environment-Wide Data Discovery (via Sentra): Use Sentra to search all relevant environments — cloud, SaaS, on-prem — for personal data tied to the individual. By using Sentra’s automated discovery and classification, Sentra can automatically identify where to search for.
- DSAR Report Generation (via Sentra): Compile a detailed report listing all personal data found and where it resides.
- Data Deletion & Verification: Remove or anonymize personal data as required, then rerun a search to verify deletion is complete.
- Final Response to Requester: Send a confirmation to the requester, outlining the actions taken and closing the request.
Sentra plays a key role in the DSAR pipeline by exposing a powerful API that enables automated, organization-wide searches for personal data. The search results can be programmatically used to trigger downstream actions like data deletion. After removal, the API can initiate a follow-up scan to verify that all data has been successfully deleted.
Benefits of DSAR Automation
With privacy regulations constantly growing, and DSAR volumes continuing to rise, building an automated, scalable pipeline is no longer a luxury - it’s a necessity.
- Automated and Cost-Efficient: Replaces costly, error-prone manual processes with a streamlined, automated approach.
- High-Speed, High-Accuracy: Sentra leverages its knowledge of where PII resides to perform targeted searches across all environments and data types, delivering comprehensive reports in hours—not days.
- Seamless Integration: A powerful API allows integration with workflow systems, enabling a fully automated, end-to-end DSAR experience for end users.
By using Sentra to intelligently locate PII across all environments, organizations can eliminate manual bottlenecks and accelerate response times. Sentra’s powerful API and deep data awareness make it possible to automate every step of the DSAR journey - from discovery to deletion - enabling privacy teams to operate at scale, reduce costs, and maintain compliance with confidence.
Turning DSAR Compliance into a Scalable Advantage with Automation
As privacy expectations grow and regulatory pressure intensifies, DSARs are no longer just a compliance checkbox, they are a reflection of how seriously an organization treats user trust. Manual, reactive processes simply cannot keep up with the scale and complexity of modern data environments, especially as personal data continues to spread across cloud, SaaS, and on-prem systems.
By automating DSAR workflows with a data-centric security platform like Sentra, organizations can respond faster, reduce compliance risk, and lower operational costs - all while freeing privacy and legal teams to focus on higher-value initiatives. In this way, DSAR compliance becomes not just a regulatory obligation, but a measure of operational maturity and a scalable advantage in building long-term trust.
<blogcta-big>

AI Governance Starts With Data Governance: Securing the Training Data and Agents Fuelling GenAI
AI Governance Starts With Data Governance: Securing the Training Data and Agents Fuelling GenAI
Generative AI isn’t just transforming products and processes - it’s expanding the entire enterprise risk surface. As C-suite executives and security leaders rush to unlock GenAI’s competitive advantages, a hard truth is clear: effective AI governance depends on solid, end-to-end data governance.
Sensitive data is increasingly used for model training and autonomous agents. If organizations fail to discover, classify, and secure these resources early, they risk privacy breaches, regulatory violations, and reputational damage. To make GenAI safe, compliant, and trustworthy from the start, data governance for generative AI needs to be a top boardroom priority.
Why Data Governance is the Cornerstone of GenAI Trustworthiness and Safety
The opportunities and risks of generative AI depend not only on algorithms, but also on the quality, security, and history of the underlying data. AWS reports that 39% of Chief Data Officers see data cleaning, integration, and storage as the main barriers to GenAI adoption, and 49% of enterprises make data quality improvement a core focus for successful AI projects (AWS Enterprise Strategy - Data Governance). Without strong data governance, sensitive information can end up in training sets, leading to unintentional leaks or model behaviors that break privacy and compliance.
Regulatory requirements, such as the Generative AI Copyright Disclosure Act, are evolving fast, raising the pressure to document data lineage and make sure unauthorized or non-compliant datasets stay out. In the world of GenAI, governance goes far beyond compliance checklists. It’s essential for building AI that is safe, auditable, and trusted by both regulators and customers.
New Attack Surfaces: Risks From Unsecured Data and Shadow AI Agents
GenAI adoption increases risk. Today, 79% of organizations have already piloted or deployed agentic AI, with many using LLM-powered agents to automate key workflows (Wikipedia - Agentic AI). But if these agents, sometimes functioning as "shadow AI" outside official oversight, access sensitive or unclassified data, the fallout can be severe.
In 2024, over 30% of AI data breaches involve insider threats or accidental disclosure, according to Quinnox Data Governance for AI. Autonomous agents can mistakenly reveal trade secrets, financial records, or customer data, damaging brand trust. The risk multiplies rapidly if sensitive data isn’t properly governed before flowing into GenAI tools. To stop these new threats, organizations need up-to-the-minute insight and control over both data and the agents using it.
Frameworks and Best Practices for Data Governance in GenAI
Leading organizations now follow data governance frameworks that match changing regulations and GenAI's technical complexity. Standards like NIST AI Risk Management Framework (AI RMF) and ISO/IEC 42001:2023 are setting the benchmarks for building auditable, resilient AI programs (Data and AI Governance - Frameworks & Best Practices).
Some of the most effective practices:
- Managing metadata and tracking full data lineage
- Using data access policies based on role and context
- Automating compliance with new AI laws
- Monitoring data integrity and checking for bias
A strong data governance program for generative AI focuses on ongoing data discovery, classification, and policy enforcement - before data or agents meet any AI models. This approach helps lower risk and gives GenAI efforts a solid base of trust.
Sentra’s Approach: Proactive Pre-Integration Discovery and Continuous Enforcement
Many tools only secure data after it’s already being used with GenAI applications. This reactive strategy leaves openings for risk. Sentra takes a different path, letting organizations discover, classify, and protect sensitive data sources before they interact with language models or agentic AI.
By using agentless, API-based discovery and classification across multi-cloud and SaaS environments, Sentra delivers immediate visibility and context-aware risk scoring for all enterprise data assets. With automated policies, businesses can mask, encrypt, or restrict data access depending on sensitivity, business requirements, or audit needs. Live Continuous monitoring tracks which AI agents are accessing data, making granular controls and fast intervention possible. These processes help stop shadow AI, keep unauthorized data out of LLM training, and maintain compliance as rules and business needs shift.
Guardrails for Responsible AI Growth Across the Enterprise
The future of GenAI depends on how well businesses can innovate while keeping security and compliance intact. As AI regulations become stricter and adoption speeds up, Sentra’s ability to provide ongoing, automated discovery and enforcement at scale is critical. Further reading: AI Automation & Data Security: What You Need To Know.
With Sentra, organizations can:
- Stop unapproved or unchecked data from being used in model training
- Identify shadow AI agents or risky automated actions as they happen
- Support audits with complete data classification
- Meet NIST, ISO, and new global standards with ease
Sentra gives CISOs, CDOs, and executives a proactive, scalable way to adopt GenAI safely, protecting the business before any model training even begins.
AI Governance Starts with Data Governance
AI governance for generative AI starts, and is won or lost, at the data layer. If organizations don’t find, classify, and secure sensitive data first, every other security measure remains reactive and ineffective. As generative AI, agent automation, and regulatory demands rise, a unified data governance strategy isn’t just good practice, it’s an urgent priority. Sentra gives security and business teams real control, making sure GenAI is secure, compliant, and trusted.
<blogcta-big>

Hybrid Environments: Expand DSPM with On-Premises Scanners
Hybrid Environments: Expand DSPM with On-Premises Scanners
Data Security Posture Management (DSPM) has quickly become a must-have for organizations moving to the cloud. By discovering, classifying, and protecting sensitive data across SaaS apps and cloud services, DSPM gave security teams visibility into data risks they never knew they had before.
But here’s the reality: most enterprises aren’t 100% cloud. Legacy file shares, private databases, and hybrid workloads still hold massive amounts of sensitive data. Without visibility into these environments, even the most advanced DSPM platforms leave critical blind spots.
That’s why DSPM platform support is evolving - from cloud-only to truly hybrid.
The Evolution of DSPM
DSPM emerged as a response to the visibility problem created by rapid cloud adoption. As organizations moved to cloud services, SaaS applications, and collaboration platforms, sensitive data began to sprawl across environments at a pace traditional security tools couldn’t keep up with. Security teams suddenly faced oversharing, inconsistent access controls, and little clarity on where critical information actually lived.
DSPM helped fill this gap by delivering a new level of insight into cloud data. It allowed organizations to map sensitive information across their environments, highlight risky exposures, and begin enforcing least-privilege principles at scale. For cloud-native companies, this represented a huge leap forward - finally, there was a way to keep up with constant data changes and movements, helping customers safely adopt the cloud while maintaining data security best practices and compliance and without slowing innovation.
But for large enterprises, the model was incomplete. Decades of IT infrastructure meant that vast amounts of sensitive information still lived in legacy databases, file shares, and private cloud environments. While DSPM gave them visibility in the cloud, it left everything else in the dark.
The Blind Spot of On-Prem & Private Data
Despite rapid cloud adoption and digital transformation progress, large organizations still rely heavily on hybrid and on-prem environments, since data movement to the cloud can be a year’s long process. On-premises file shares such as NetApp ONTAP, SMB, and NTFS, alongside enterprise databases like Oracle, SQL Server, and MySQL, remain central to operations. Private cloud applications are especially common in regulated industries like healthcare, finance, and government, where compliance demands keep critical data on-premises.
To scan on premises data, many DSPM providers offer partial solutions by taking ephemeral ‘snapshots’ of that data and temporarily moving it to the cloud (either within customer environment, as Sentra does, or to the vendor cloud as some others do) for classification analysis. This can satisfy some requirements, but often is seen as a compliance risk for very sensitive or private data which must remain on-premises. What’s left are two untenable alternatives - ignoring the data which leaves serious visibility gaps or utilizing manual techniques which do not scale.
These approaches were clearly not built for today’s security or operational requirements. Sensitive data is created and proliferates rapidly, which means it may be unclassified, unmonitored, and overexposed, but how do you even know? From a compliance and risk standpoint, DSPM without on-prem visibility is like watching only half the field, and leaving the other half open to attackers or accidental exposure.
Expanding with On-Prem Scanners
Sentra is changing the equation. With the launch of its on-premise scanners, the platform now extends beyond the cloud to hybrid and private environments, giving organizations a single pane of glass for all their data security.
With Sentra, organizations can:
- Discover and classify sensitive data across traditional file shares (SMB, NFS, CIFS, NTFS) and enterprise databases (Oracle, SQL Server, MySQL, MSSQL, PostgreSDL, MongoDB, MariaDB, IBM DB2, Teradata).
- Detects and protects critical data as it moves between on-prem and cloud environments.
- Apply AI-powered classification and enforce Microsoft Purview labeling consistently across environments.
- Strengthen compliance with frameworks that demand full visibility across hybrid estates.
- Have a choice of deployment models that best fits their security, compliance, and operational requirements.
Crucially, Sentra’s architecture allows customers to ensure private data always remains in their own environment. They need not move data outside their premises and nothing is ever copied into Sentra’s cloud, making it a trusted choice for enterprises that require secure, private data processing.
Extending the Hybrid Vision
This milestone builds on Sentra’s proven track record as the only cloud-native data security platform that guarantees data always remains within the customer’s cloud environments - never copied or stored in Sentra’s cloud.
Now, Sentra’s AI-powered classification and governance engine can also be deployed in organizations that require onsite data processing, giving them the flexibility to protect both structured and unstructured data across cloud and on-premises systems.
By unifying visibility and governance across all environments while maintaining complete data sovereignty, Sentra continues to lead the next phase of DSPM, one built for modern, hybrid enterprises.
Real-World Impact
Picture a global bank: with modern customer-facing websites and mobile applications hosted in the public cloud, providing agility and scalability for digital services. At the same time, the bank continues to rely on decades-old operational databases running in its private cloud — systems that power core banking functions such as transactions and account management. Without visibility into both, security teams can’t fully understand the risks these stores may pose and enforce least privilege, prevent oversharing, or ensure compliance.
With hybrid DSPM powered by on-prem scanners, that same bank can unify classification and governance across every environment - cloud or on-prem, and close the gaps that attackers or AI systems could otherwise exploit.
Conclusion
DSPM solved the cloud problem. But enterprises aren’t just in the cloud, they’re hybrid. Legacy systems and private environments still hold critical data, and leaving them out of your security posture is no longer an option.
Sentra’s on-premise scanners mark the next stage of DSPM evolution: one unified platform for cloud, on-prem, and private environments. With full visibility, accurate classification, and consistent governance, enterprises finally have the end-to-end data security they need for the AI era. Because protecting half your data is no longer enough.
<blogcta-big>

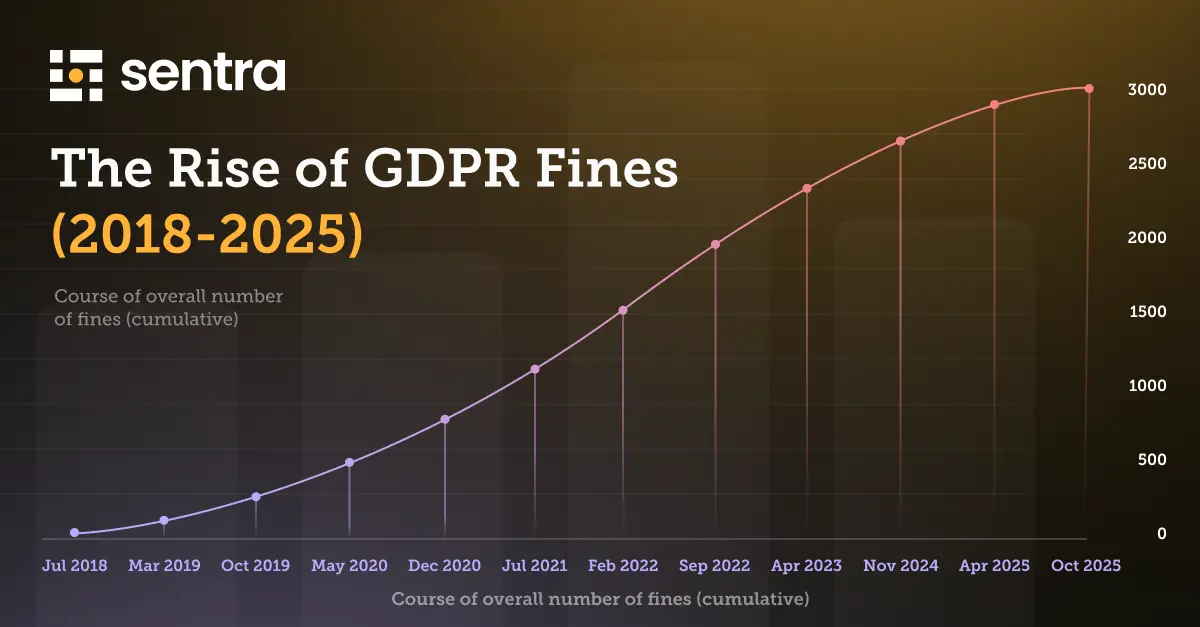
GDPR Compliance Failures Lead to Surge in Fines
GDPR Compliance Failures Lead to Surge in Fines
In recent years, the landscape of data privacy and protection has become increasingly stringent, with regulators around the world cracking down on companies that fail to comply with local and international standards.
The latest high-profile case involves TikTok, which was recently fined a staggering €530 million ($600 million) by the Irish Data Protection Commission (DPC) for violations related to the General Data Protection Regulation (GDPR). This is a wake up call for multinational companies.
What is GDPR?
The General Data Protection Regulation (GDPR) is a data protection law that came into effect in the EU in May 2018. Its goal is to give individuals more control over their personal data and unify data protection rules across the EU.
GDPR gives extra protection to special categories of sensitive data. Both 'controllers' (who decide how data is processed) and 'processors' (who act on their behalf) must comply. Joint controllers may share responsibility when multiple entities manage data.
Who Does the GDPR Apply To?
GDPR applies to both EU-based and non-EU organizations that handle the data of EU residents. The regulation requires organizations to obtain clear consent for data collection and processing, and it gives individuals rights to access, correct, and delete their data. Organizations must also ensure strong data security and report any data breaches promptly.
What Are Data Subject Access Requests (DSARs)?
One of the core rights granted to individuals under GDPR is the ability to understand and control how their personal data is used. This is made possible through Data Subject Access Requests (DSARs).
A DSAR allows any EU resident to request access to the personal data an organization holds about them. In response, the organization must provide a comprehensive overview, including:
- What personal data is being processed
- The purpose of processing
- Data sources and recipients
- Retention periods
- Information about automated decision-making
Organizations are required to respond to DSARs within one month, making them a time-sensitive and resource-intensive obligation, especially for companies with complex data environments.
What Are the Penalties for Non-Compliance with GDPR?
Non-compliance with the General Data Protection Regulation (GDPR) can result in substantial penalties.
Article 83 of the GDPR establishes the fine framework, which includes the following:
Maximum Fine: The maximum fine for GDPR non-compliance can reach up to 20 million euros, or 4% of the company’s total global turnover from the preceding fiscal year, whichever is higher.
Alternative Penalty: In certain cases, the fine may be set at 10 million euros or 2% of the annual global revenue, as outlined in Article 83(4).
Additionally, individual EU member states have the authority to impose their own penalties for breaches not specifically addressed by Article 83, as permitted by the GDPR’s flexibility clause.
So far, the maximum fine given under GDPR was to Meta in 2023, which was fined $1.3 billion for violating GDPR laws related to data transfers. We’ll delve into the details of that case shortly.
Can Individuals Be Fined for GDPR Breaches?
While fines are typically imposed on organizations, individuals can be fined under certain circumstances. For example, if a person is self-employed and processes personal data as part of their business activities, they could be held responsible for a GDPR breach. However, UK-GDPR and EU-GDPR do not apply to data processing carried out by individuals for personal or household activities.
According to GDPR Chapter 1, Article 4, “any natural or legal person, public authority, agency, or body” can be held accountable for non-compliance. This means that GDPR regulations do not distinguish significantly between individuals and corporations when it comes to breaches.
Specific scenarios where individuals within organizations may be fined include:
- Obstructing a GDPR compliance investigation.
- Providing false information to the ICO or DPA.
- Destroying or falsifying evidence or information.
- Obstructing official warrants related to GDPR or privacy laws.
- Unlawfully obtaining personal data without the data controller's permission.
The Top 3 GDPR Fines and Their Impact
1. Meta - €1.2 Billion ($1.3 Billion), 2023
In May 2023, Meta, the U.S. tech giant, was hit with a staggering $1.3 billion fine by an Irish court for violating GDPR regulations concerning data transfers between the E.U. and the U.S. This massive penalty came after the E.U.-U.S. Privacy Shield Framework, which previously provided legal cover for such transfers, was invalidated in 2020. The court found that the framework failed to offer sufficient protection for EU citizens against government surveillance. This fine now stands as the largest ever under GDPR, surpassing Amazon’s 2021 record.
2. Amazon - €746 million ($781 million), 2021
Which leads us to Amazon at number 2, not bad. In 2021, Amazon Europe received the second-largest GDPR fine to date from Luxembourg’s National Commission for Data Protection (CNPD). The fine was imposed after it was determined that the online retailer was storing advertisement cookies without obtaining proper consent from its users.
3. TikTok – €530 million ($600 million), 2025
The Irish Data Protection Commission (DPC) fined TikTok for failing to protect user data from unlawful access and for violating GDPR rules on international data transfers in May 2025. The investigation found that TikTok allowed EU users’ personal data to be accessed from China without ensuring adequate safeguards, breaching GDPR’s requirements for cross-border data protection and transparency. The DPC also cited shortcomings in how TikTok informed users about where their data was processed and who could access it. The case reinforced regulators’ focus on international data transfers and children’s privacy on social media platforms.
The Implications for Global Companies
The growing frequency of such fines sends a clear message to global companies: compliance with data protection regulations is non-negotiable. As European regulators continue to enforce GDPR rigorously, companies that fail to implement adequate data protection measures risk facing severe financial penalties and reputational harm.
In the case of Uber, the company’s failure to use appropriate mechanisms for data transfers, such as Standard Contractual Clauses, led to significant repercussions. This situation emphasizes the importance of staying current with regulatory changes, such as the introduction of the E.U.-U.S. Data Privacy Framework, and ensuring that all data transfer practices are fully compliant.
How Sentra Helps Organizations Stay Compliant with GDPR
Sentra helps organizations maintain GDPR compliance by effectively tagging data belonging to European citizens.
When EU citizens' Personally Identifiable Information (PII) is moved or stored outside of EU data centers, Sentra will detect and alert you in near real-time. Our continuous monitoring and scanning capabilities ensure that any data violations are identified and flagged promptly.

Unlike traditional methods where data replication can obscure visibility and lead to issues during audits, Sentra provides ongoing visibility into data storage. This proactive approach significantly reduces the risk by alerting you to potential compliance issues as they arise.
Sentra does automatic classification of localized data - specifically in this case, EU data. Below you can see an example of how we do this.

The Rise of Compliance Violations: A Wake-up Call
The increasing number of compliance violations and the related hefty fines should serve as a wake-up call for companies worldwide. As the regulatory environment becomes more complex, it is crucial for organizations to prioritize data protection and privacy. By doing so, they can avoid costly penalties and maintain the trust of their customers and stakeholders.
Solutions such as Sentra provide a cost-effective means to ensure sensitive data always has the right posture and security controls - no matter where the data travels - and can alert on exceptions that require rapid remediation. In this way, organizations can remain regulatory compliant, avoid the steep penalties for violations, and ensure the proper, secure use of data throughout their ecosystem.
To learn more about how Sentra's Data Security Platform can help you stay compliant, avoid GDPR penalties, and ensure the proper, secure use of data, request a demo today.
<blogcta-big>
.webp)

Sentra Achieves TX-RAMP Certification: Demonstrating Leadership in Data Security Compliance
Sentra Achieves TX-RAMP Certification: Demonstrating Leadership in Data Security Compliance
Introduction
We’re excited to announce that Sentra has officially achieved TX-RAMP certification, a significant milestone that underscores our commitment to delivering trusted, compliant, and secure cloud data protection.
The Texas Risk and Authorization Management Program (TX-RAMP) establishes rigorous security standards for cloud products and services used by Texas state agencies. Achieving this certification validates that Sentra meets and exceeds these standards, ensuring our customers can confidently rely on our platform to safeguard sensitive data.
For agencies and organizations operating in Texas, this means streamlined procurement, faster adoption, and the assurance that Sentra’s solutions are fully aligned with state-mandated compliance requirements. For our broader customer base, TX-RAMP certification reinforces Sentra’s role as a trusted leader in data security posture management (DSPM) and our ongoing dedication to protecting data everywhere it lives.
What is TX-RAMP?
The Texas Risk and Authorization Management Program (TX-RAMP) is the state’s framework for evaluating the security of cloud solutions used by public sector agencies. Its goal is to ensure that organizations working with Texas state data meet strict standards for risk management, compliance, and operational security.
TX-RAMP certification focuses on key areas such as:
- Audit & Accountability: Ensuring system activity is monitored, logged, and reviewed.
- System Integrity: Protecting against malicious code and emerging threats.
- Access Control: Managing user accounts and privileges with least-privilege principles.
- Policy & Governance: Establishing strong security policies and updating them regularly.
By certifying vendors, TX-RAMP helps agencies reduce risk, streamline procurement, and ensure sensitive state and citizen data is well protected.
Why TX-RAMP Certification Matters
For Texas agencies, TX-RAMP certification means trust and speed. Working with a certified partner like Sentra simplifies procurement, reduces onboarding time, and provides confidence that solutions meet the state’s toughest security requirements.
For enterprises and organizations outside Texas, this milestone is just as meaningful. TX-RAMP certification validates that Sentra’s DSPM platform can meet and go beyond some of the most demanding compliance frameworks in the U.S. It’s another proof point that when customers choose Sentra, they are choosing a solution built with security, accountability, and transparency at its core.
Sentra’s Path to TX-RAMP Certification
Achieving TX-RAMP certification required proving that Sentra’s security controls align with strict state requirements.
Some of the measures that demonstrate compliance include:
- Audit and Accountability: Continuous monitoring and quarterly reviews of audit logs under SOC 2 Type II governance.
- System and Information Integrity: Endpoint protection and weekly scans to prevent, detect, and respond to malicious code.
- Access Control: Strong account management practices using Okta, BambooHR, MFA, and quarterly access reviews.
- Change Management and Governance: Structured SDLC processes with documented requests, multi-level approvals, and complete audit trails.
Together, these safeguards show that Sentra doesn’t just comply with TX-RAMP - we exceed the requirements, embedding security into every layer of our operations and platform.
What This Means for Sentra Customers
For Texas agencies, TX-RAMP certification makes it easier and faster to adopt Sentra’s platform, knowing that it has already been vetted against the state’s most stringent standards.
For global enterprises, it’s another layer of assurance: Sentra’s DSPM solution is designed to stand up to the highest levels of compliance practice, giving customers confidence that their most sensitive data is secure - wherever it lives.
Conclusion
Earning TX-RAMP certification is a major milestone in Sentra’s journey, but it’s only part of our broader mission: building trust through security, compliance, and innovation.
This recognition reinforces Sentra’s role as a leader in data security posture management (DSPM) and gives both public sector and private enterprises confidence that their data is safeguarded by a platform designed for the most demanding environments.
<blogcta-big>

NYDFS 2.0: New Cybersecurity Requirements and Enforcement
NYDFS 2.0: New Cybersecurity Requirements and Enforcement
NYDFS Steps Up Enforcement
The New York State Department of Financial Services (NYDFS) has long been one of the most influential regulators in the financial sector, but over the past two years, it’s made one thing crystal clear: cybersecurity is no longer a back-office IT concern, it’s a regulatory priority.
In response to growing threats, increasing reliance on third-party services, and persistent operational risks, NYDFS has tightened its expectations around how financial institutions protect sensitive data. And it’s backing that stance with real financial consequences.
Just ask PayPal or OneMain Financial, two major firms hit with multimillion-dollar penalties for cybersecurity lapses. These weren’t headline-grabbing breaches or ransomware attacks, they were the result of basic control failures, delayed reporting, and repeated gaps in governance.
What do a $2M fine for PayPal and a $4.25M penalty for OneMain have in common?
Weak cybersecurity practices, and a regulator that’s no longer willing to wait for companies to catch up.
The Recent Crackdowns: PayPal and OneMain
a. PayPal – $2M Civil Penalty (January 2025)
In January 2025, NYDFS announced a $2 million penalty against PayPal for violations of its cybersecurity regulations under Part 500. The enforcement focused on failures to report a cybersecurity event in a timely manner and gaps in maintaining certain required controls.
The incident involved unauthorized access to over 34,000 user accounts, exposing sensitive personal data including tax IDs and financial information. NYDFS emphasized that PayPal’s delayed reporting and lack of specific security measures put both consumers and the broader financial ecosystem at risk.
What it signals: No company - not even a digital-native fintech giant is immune from enforcement. The bar is rising, and NYDFS is expecting organizations to report, respond, and remediate swiftly and transparently.
b. OneMain Financial – $4.25M Fine (May 2023)
In May 2023, NYDFS fined OneMain Financial $4.25 million after discovering systemic cybersecurity deficiencies, including improperly stored passwords, insufficient multi-factor authentication, and inadequate third-party risk management.
Even more concerning: many of these issues were identified in earlier audits and hadn’t been fully addressed. NYDFS made it clear that repeated inaction wouldn’t be tolerated.
What it signals: It’s not just about responding to one-off incidents — regulators are watching for long-term security maturity. Ongoing hygiene, policy enforcement, and consistent control testing are now table stakes.
What’s Changing: NYDFS 2.0 (Part 500 Amendments)
These enforcement actions aren’t just about past violations, they’re a preview of what’s to come.
With the rollout of the NYDFS Second Amendment to Part 500, also known as NYDFS 2.0, covered entities, especially those classified as Class A companies are facing a new set of enforceable expectations.
Key new requirements include:
- Annual independent audits of cybersecurity programs
- Mandatory multi-factor authentication (MFA) for all systems
- Stronger access control policies, including role-based access
- Board-level or senior executive oversight of cybersecurity governance
Full enforcement kicks in on November 1, 2025. At that point, these aren’t just checkboxes, they’re compliance requirements with real financial and reputational risk for falling short.
The message is clear: NYDFS is no longer satisfied with written policies and best-effort intentions. It's expecting demonstrated outcomes, measurable control, and leadership accountability.
The Broader Message: Enforcement Is the New Default
NYDFS isn’t the only regulator stepping up, but it’s arguably the most proactive, and most willing to act. These recent fines signal a broader shift across the industry: compliance is no longer about having good intentions or written policies. Regulators are now focused on evidence of execution, real controls, timely reporting, and provable outcomes.
In other words, enforcement is the new default. This shift reframes cybersecurity from a purely technical issue to a board-level governance challenge. It's not enough for IT or security teams to manage risk in isolation. Executive leadership, legal, and compliance functions all need to be aligned — and accountable.
If your organization is treating cybersecurity as just a tech responsibility, you’re behind.
What Organizations Should Do Now
The message from regulators is clear, and now is the time to act.
Here are four practical steps your team can take to stay ahead:
- Audit your current posture against NYDFS Part 500. Focus especially on:
- Incident reporting timelines
- MFA coverage
- Access controls
- Third-party risk assessments
- Incident reporting timelines
- Prioritize visibility across your environment
You can’t protect what you can’t see. Ensure you have continuous insight into where sensitive data lives, who can access it, and how it moves across cloud, SaaS, and on-prem systems. - Document everything
Have clear records of your policies, security controls, vendor assessments, incident response processes, and risk decisions. If you had to prove your compliance tomorrow, could you? - Benchmark your controls against recent enforcement
If PayPal and OneMain were fined for these issues, ask yourself:
How would our program hold up under similar scrutiny?
Final Thoughts: Read the Signals Now, Not After a Fine
The writing is on the wall - NYDFS is raising the bar, and other regulators are likely to follow. This is your opportunity to get ahead of the curve, rather than scrambling after the fact.
Take these fines as what they are: a warning shot and a roadmap. Organizations that prepare now - with tighter controls, better visibility, and cross-functional ownership won’t just avoid penalties. They’ll be more resilient, more trusted, and better equipped to lead in a high-risk landscape.
If you’re not sure where to start, use these enforcement cases as a prompt for an internal review. And if you want to go deeper, we’ve put together a compliance checklist that can help you assess where you stand.
Better to find the gaps now before NYDFS does.
<blogcta-big>


What the HIPAA Compliance Updates Mean for Your Security
What the HIPAA Compliance Updates Mean for Your Security
The Health Insurance Portability and Accountability Act (HIPAA) has long been a cornerstone of safeguarding sensitive health information in the U.S., particularly electronic protected health information (ePHI). As healthcare organizations continue to face growing cybersecurity challenges, ensuring the protection of ePHI has never been more critical.
In response, for the first time in two decades, the U.S. Department of Health and Human Services (HHS) has proposed significant amendments to the HIPAA Security Rule, aimed at strengthening cybersecurity measures across the healthcare sector. These proposed changes are designed to address emerging threats and ensure that healthcare organizations have robust systems in place to protect patient data from unauthorized access and potential breaches. This blog presents the major changes that are coming soon and how you can prepare for them.
Instead of considering compliance as a one-time effort, with Sentra you can monitor your compliance status at any given moment, streamline reporting, and remediate compliance violations instantly.
How Sentra Can Help You Stay Compliant
Sentra’s data security platform equips healthcare organizations with the necessary tools to stay compliant with the new HIPAA Security Rule amendments. By providing continuous monitoring of ePHI data locations and assessing associated risks, Sentra helps organizations maintain full visibility and control over sensitive data.
Key Benefits of Using Sentra for HIPAA Compliance:
- Automated Data Discovery & Classification: Instantly locate and classify ePHI across cloud and on-prem environments.
- Real-time Risk Assessment: Continuously assess vulnerabilities and flag security gaps related to HIPAA requirements.
- Access Control & Encryption Monitoring: Ensure compliance with mandatory MFA, encryption policies, and access termination requirements.
- Smart Compliance Alerts: Sentra doesn’t just detect generic cloud misconfigurations. Instead, it pinpoints security issues affecting sensitive data, helping teams focus on what truly matters.
Without a solution such as Sentra, organizations waste valuable time manually searching for and classifying sensitive data, diverting key employees from higher-priority security tasks. With Sentra, security teams gain an ongoing, real-time dashboard that ensures efficient compliance and faster risk mitigation.
What You Need to Know About the Proposed HIPAA Security Rule Updates
The latest proposed updates to the HIPAA Security Rule represent some of the most significant changes in years. These updates aim to modernize data protection practices and ensure healthcare organizations are better equipped to handle today’s security challenges. Below are the key highlights compliance and security teams should focus on:
Mandatory Implementation Specifications
All implementation specifications under the HIPAA Security Rule will become mandatory. Covered entities and business associates must now fully comply with all safeguards—no more "addressable" exceptions.
Stricter Encryption Requirements
Encryption of electronic protected health information (ePHI) will be required both at rest and in transit. Organizations must ensure encryption is in place across all systems handling sensitive data.
Required Multifactor Authentication (MFA)
MFA will become mandatory to protect access to ePHI. This added security layer significantly reduces the risk of unauthorized access and credential compromise.
Network Segmentation for Threat Containment
Organizations must implement network segmentation to isolate sensitive systems and limit the spread of cyber threats in the event of a breach.
Timely Termination of Access
Access to ePHI must be revoked within 24 hours when an employee leaves or changes roles. This reduces the risk of insider threats and unauthorized access.
Comprehensive Documentation Requirements
Healthcare organizations must maintain detailed, up-to-date documentation of all security policies, procedures, risk assessments, and incident response plans.
Asset Inventories and Network Mapping
Annual updates to technology asset inventories and network maps will be required to ensure accurate tracking of where and how ePHI is stored and transmitted.
Enhanced Risk Analysis
Organizations must conduct regular, thorough risk assessments to identify vulnerabilities and assess threats across all systems that interact with ePHI.
Stronger Incident Response Plans
Entities must be able to restore lost systems and data within 72 hours after a cyber incident. Regular testing and refinement of incident response protocols will be essential.
Annual Compliance Audits
Healthcare organizations will be required to conduct annual audits of their HIPAA Security Rule compliance, covering all technical and administrative safeguards.
Mandatory Technical Controls
Technical safeguards like anti-malware tools, firewalls, and port restrictions must be in place and regularly reviewed to protect systems from evolving threats.
What’s Next?
The proposed changes to the HIPAA Security Rule are currently in the Notice of Proposed Rulemaking (NPRM) stage, with a 60-day public comment period that opened on January 6, 2025. During this period, stakeholders can provide feedback on the amendments, which may influence the final rule. Organizations should actively monitor the comment period, engage in the feedback process, and stay informed on any potential adjustments before the rule is finalized.
Steps Organizations Should Take Now:
- Review the proposed changes and understand how they impact your current security posture.
- Engage in the public comment process to share concerns or recommendations.
- Start assessing security gaps to align with HIPAA’s evolving compliance requirements.
Conclusion
The new HIPAA compliance amendments represent a major shift in how healthcare organizations must protect electronic Protected Health Information (ePHI). The introduction of enhanced encryption standards, mandatory multi-factor authentication (MFA), and stricter access control measures means organizations must act swiftly to maintain compliance and reduce cybersecurity risks.
Compliance is not just about meeting regulations, it is about efficiency. Organizations relying on manual processes to locate and secure sensitive data waste valuable time and resources, making compliance efforts less effective.
With Sentra, healthcare organizations gain a powerful, automated data security solution that:
- Eliminates manual data discovery by providing a real-time, continuous inventory of sensitive data.
- Prioritizes relevant data security risks instead of overwhelming teams with unnecessary alerts.
- Ensures compliance readiness by automating key processes like access control monitoring and encryption verification.
Now is the time for healthcare organizations to take proactive steps toward compliance. Stay informed, participate in the public comment process, and start implementing security enhancements today.
To learn how Sentra can help your organization achieve HIPAA compliance efficiently, request a demo today and take control of your sensitive data.
<blogcta-big>

The Need for Continuous Compliance
The Need for Continuous Compliance
As compliance breaches rise and hefty fines follow, establishing and maintaining strict compliance has become a top priority for enterprises. However, compliance isn't a one-time or even periodic task or something you can set and forget. To stay ahead, organizations are embracing continuous compliance - a proactive, ongoing strategy to meet regulatory requirements and uphold security standards.
Let’s explore what continuous compliance is, the advantages it offers, some challenges it may present, and how Sentra can help organizations achieve and sustain it.
What is Continuous Compliance?
Continuous compliance is the ongoing process of monitoring a company’s security practices and applying appropriate controls to ensure they consistently meet regulatory standards and industry best practices. Instead of treating compliance as a one-time task, it involves real-time monitoring and advanced data protection strategies to catch and address non-compliance issues as they happen. It also includes maintaining a complete inventory of where your data is at all times, what risks and security posture is associated, and who has access to it. This proactive approach, including continuous compliance testing to verify controls are working effectively, ensures you are always ‘audit ready’ and helps avoid last-minute fixes before audits or cyber attacks., ensuring The result is continuous security across the organization.
Why Do Companies Need Continuous Compliance?
Continuous compliance is essential for companies to ensure they are always aligned with industry regulations and standards, reducing the risk of violations and penalties.
Here are a few key reasons why it's crucial:
- Regulatory Changes: Compliance standards frequently evolve. Continuous compliance monitoring ensures companies can adapt quickly to new regulations without major disruptions.
- Avoiding Fines and Penalties: Non-compliance can lead to hefty fines and regulatory enforcement, legal actions or even loss of licenses. Staying compliant helps avoid these risks.
- Protecting Reputation: Data breaches, especially in industries dealing with sensitive data, can damage a company’s reputation. Continuous compliance helps protect established trust with customers, partners, and stakeholders.
- Reducing Security Risks: Many compliance frameworks are designed to enhance data security. Continuous compliance works alongside automated remediation capabilities to keep a company’s security posture is always up-to-date, reducing the risk of data breaches.
- Operational Efficiency: Automated, continuous compliance monitoring can streamline processes, reducing manual audits and interventions, saving time and resources.
For modern businesses, especially those managing sensitive data in the cloud, a continuous cloud compliance strategy is critical to maintaining a secure, efficient, and trusted operation.
Cost Considerations for Compliance Investments
Investing in continuous compliance can lead to significant long-term savings. By maintaining consistent compliance practices, organizations can avoid the hefty fines associated with non-compliance, minimize resource surges during audits, and reduce the impacts of breaches through early detection. Continuous compliance provides security and financial predictability, often resulting in more manageable and predictable expenses.
In contrast, periodic compliance can lead to fluctuating costs. While expenses may be lower between audits, costs typically spike as audit dates approach. These spikes often result from hiring consultants, deploying temporary tools, or incurring overtime charges. Moreover, gaps between audits increase the risk of undetected non-compliance or security breaches, potentially leading to significant unplanned expenses from fines or mitigation efforts.
When evaluating cost implications, it's crucial to look beyond immediate expenses and consider the long-term financial impact. Continuous compliance not only offers a steadier expenditure pattern but also potential savings through proactive measures. On the other hand, periodic compliance can introduce cost variability and financial uncertainties associated with risk management.
Challenges of Continuous Compliance
- Keeping Pace with Technological Advancements: The fast-evolving tech landscape makes compliance a moving target. Organizations need to regularly update their systems to stay in line with new technology, ensuring compliance procedures remain effective. This requires investment in infrastructure that can adapt quickly to these changes. Additionally, keeping up with emerging security risks requires continuous threat detection and response strategies, focusing on real-time compliance monitoring and adaptive security standards to safeguard against new threats.
- Data Privacy and Protection Across Borders: Global organizations face the challenge of navigating multiple, often conflicting, data protection regulations. To maintain compliance, they must implement unified strategies that respect regional differences while adhering to international standards. This includes consistent data sensitivity tagging and secure data storage, transfer, and processing, with measures like encryption and access controls to protect sensitive information.
- Internal Resistance and Cultural Shifts: Implementing continuous compliance often meets internal resistance, requiring effective change management, communication, and education. Building a compliance-oriented culture, where it’s seen as a core value rather than a box-ticking exercise, is crucial.
Organizations must be adaptable, invest in the right technology, and create a culture that embraces compliance. This both helps meet regulatory demands and also strengthens risk management and security resilience.
How You Can Achieve Continuous Compliance With Sentra
First, Sentra's automated data discovery and classification engine and takes a fraction of the time and effort it would take to manually catalog all sensitive data. It’s far more accurate, especially when using a solution that leverages LLMs to classify data with more granularity and rich context. It’s also more responsive to the frequent changes in your modern data landscape.
Sentra also can automate the process of identifying regulatory violations and ensuring adherence to compliance requirements using pre-built policies that update and evolve with compliance changes (including policies that map to common compliance frameworks). It ensures that sensitive data stays within the correct environments and doesn’t travel to regions in violation of retention policies or without data encryption.

In contrast, manually tracking data inventory is inefficient, difficult to scale, and prone to errors and inaccuracies. This often results in delayed detection of risks, which can require significant time and effort to resolve as compliance audits approach.
<blogcta-big>

Data Loss Prevention for Google Workspace
Data Loss Prevention for Google Workspace
We know that Google Workspace (formerly known as G Suite) and its assortment of services, including Gmail, Drive, Calendar, Meet, Docs, Sheets, Slides, Chat, and Vids, is a powerhouse for collaboration.
But the big question is: Do you know where your Google Workspace data is—and if it’s secure and who has access to it?
While Google Workspace has become an indispensable pillar in cloud operations and collaboration, its widespread adoption introduces significant security risks that businesses simply can't afford to ignore. To optimize Google Workspace data protection, enterprises must know how Google Workspace protects and classifies data. Knowing the scope, gaps, limitations, and silos of Google Workspace data protection mechanisms can help businesses strategize more effectively to mitigate data risks and ensure more holistic data security coverage across multi-cloud estates.
The Risks of Google Workspace Security
As with any dynamic cloud platform, Google Workspace is susceptible to data security risks, the most dangerous of which can do more than just undercut its benefits. Primarily, businesses should be concerned about the exposure of sensitive data nested within large volumes of unstructured data. For instance, if an employee shares a Google Drive folder or document containing sensitive data but with suboptimal access controls, it could snowball into a large-scale data security disaster.
Without comprehensive visibility into sensitive data exposures across Google Workspace applications, businesses risk serious security threats. Besides sensitive data exposure, these include exploitable vulnerabilities, external attacks, human error, and shadow data. Complex shared responsibility models and unmet compliance policies also loom large, threatening the security of your data.
To tackle these risks, businesses must prioritize and optimize data security across Google Workspace products while acknowledging that Google is rarely the sole platform an enterprise uses.
How Does Google Store Your Data?
To understand how to protect sensitive data in Google Workspace, it's essential to first examine how Google stores and manages this data. Why? Because the intricacies of data storage architectures and practices have significant implications for your security posture.
Here are three-steps to help you understand and optimize your data storage in Google Workspace:
1. Know Where and How Google Stores Your Data
- Google stores your files in customized servers in secure data centers.
- Your data is automatically distributed across multiple regions, guaranteeing redundancy and availability.
2. Control Data Retention
- Google retains your Workspace data until you or an admin deletes it.
- Use Google Vault to manage retention policies and set custom retention rules for emails and files.
- Regularly review and clean up unnecessary stored data to reduce security risks.
3. Secure Your Stored Data
- Enable encryption for sensitive files in Google Drive.
- Restrict who can view, edit, and share stored documents by implementing access controls.
- Monitor data access logs to detect unauthorized access.
How Does Google Workspace Classify Your Data?
Google’s built-in classification tools are an acceptable starting point. However, they fall short of securing and classifying all unstructured data across complex cloud environments. This is because today's cloud attack surface expands across multiple providers, making security more complex than ever before. Consequently, Google's myopic classification often snowballs into bigger security problems, as data moves. Because of this evolving attack surface across multi-cloud environments, risk-ridden shadow data and unstructured data fester in Google Workspace apps.
The Issue of Unstructured Data
It’s important to remember that most enterprise data is unstructured. Unstructured data refers to data that isn’t stored in standardized or easily manageable formats. In Google Workspace, this could be data in a Gmail draft, multimedia files in Google Drive, or other informal exchanges of sensitive information between Workspace apps.
For years, unstructured data has been a nightmare for businesses to map, manage, and secure. Unstructured document stores and employee GDrives are hot zones for data risks. Native Google Drive data classification capabilities can be a useful source of metadata to support a more comprehensive external data classification solution. A cloud-native DSP solution can map, classify, and organize sensitive data, including PHI, PCI, and business secrets, across both Google Workspace and cloud platforms that Google's built-in capabilities do not cover, like AWS and S3.
How Does Google Workspace Protect Your Data?
Like its built-in classification mechanisms, Google's baseline security features, such as encryption and access controls, are good for simple use cases but aren't capable enough to fully protect complex environments.
For both the classification and security of unstructured data, Google’s native tools may not suffice. A robust data loss prevention (DLP) solution should ideally do the trick for unstructured data. However, Google Workspace DLP alone and other protection measures (formerly referred to as G Suite data protection) are unlikely to provide holistic data security, especially in dynamic cloud environments.
Google Native Tool Challenges
Google’s basic protection measures don't tackle the full spectrum of critical Google Workspace data risks because they can't permeate unstructured documents, where sensitive data may reside in various protected states.
For example, an employee's personal Google Drive can potentially house exposed and exploitable sensitive data that can slip through Google's built-in security mechanisms. It’s also important to remember that Google Workspace data loss prevention capabilities do nothing to protect critical enterprise data hosted in other cloud platforms.
Ultimately, while Google provides some security controls, they alone don’t offer the level of protection that today’s complex cloud environments demand. To close these gaps, businesses must look to complement Google’s built-in capabilities and invest in robust data security solutions.
Only a highly integrable data security tool with advanced AI and ML capabilities can protect unstructured data across Google Workspace’s diverse suite of apps, and further, across the entire enterprise data estate. This has become mandatory since multi-cloud architectures are the norm today.
A Robust Data Security Platform: The Key to Holistic Google Workspace Data Protection
The speed, complexity, and rapid evolution of multi-cloud and hybrid cloud environments demand more advanced data security capabilities than Google Workspace’s native storage, classification, and protection features provide.
It is becoming increasingly difficult to mitigate the risks associated with sensitive data.
To successfully remediate these risks, businesses urgently need robust data security posture management (DSPM) and data detection and response (DDR) solutions - preferably all in one platform. There's simply no other way to guarantee comprehensive data protection across Google Workspace. Furthermore, as mentioned earlier, most businesses don't exclusively use Google platforms. They often mix and match services from cloud providers like Google, Azure, and AWS.
In other words, besides limited data classification and protection, Google's built-in capabilities won't be able to extend into other branches of an enterprise's multi-cloud architecture. And having siloed data security tools for each of these cloud platforms increases costs and further complicates administration that can lead to critical coverage gaps. That's why the optimal solution is a holistic platform that can fill the gaps in Google's existing capabilities to provide unified data classification, security, and coverage across all other cloud platforms.
Sentra: The Ultimate Cloud-Agnostic Data Protection and Classification Solution
To truly secure sensitive data across Google Workspace and beyond, enterprises need a cloud-native data security platform. That’s where Sentra comes in. It hands you enterprise-scale data protection by seamlessly integrating powerful capabilities like data discovery and classification, data security posture management (DSPM), data access governance (DAG), and data detection and response (DDR) into an all-in-one, easy-to-use platform.
By combining rule-based and large language model (LLM)-based classification, Sentra ensures accurate and scalable data security across Workspace apps like Google Drive—as well as data contained in apps from other cloud providers. This is crucial for any enterprise that hosts its data across disparate cloud platforms, not just Workspace. To classify unstructured data across these platforms, Sentra leverages supervised AI training models like BERT. It also uses zero-shot classification techniques to zero in on and accurately classify unstructured data.
Sentra is particularly useful for anyone asking business-, industry-, or geography-specific data security questions such as “Does Google Workspace have HIPAA compliance frameworks?” and “Is my organization's use of Google Workspace GDPR-compliant?” The short answer to these questions: Integrate Sentra with your Google Workspace apps and you will see.
Boost Your Google Workspace Data Protection with Sentra
By integrating Sentra with Google Workspace, companies can leverage AI-driven insights to distinguish employee data from customer data, ensuring a clearer understanding of their information landscape. Sentra also identifies customer-specific data types, such as personally identifiable information (PII), protected health information (PHI), product IDs, private codes, and localization requirements. Additionally, it detects toxic data combinations that may pose security risks.
Beyond insights, Sentra provides robust data protection through comprehensive inventorying and classification of unstructured data. It helps organizations right-size permissions, expose shadow data, and implement real-time detection of sensitive data exposure, security breaches, and suspicious activity, ensuring a proactive approach to data security.
No matter where your unstructured data resides, whether in Google Drive or any other cloud service, Sentra ensures it is accurately identified, classified, and protected with over 95% precision.
If you’re ready to take control of your data security, book a demo to discover how Sentra’s AI-driven protection secures your most valuable information across Google Workspace and beyond.
<blogcta-big>

Understanding the FTC Data Breach Reporting Requirements
Understanding the FTC Data Breach Reporting Requirements
More Companies Need to Report Data Breaches
In a significant move towards enhancing data security and transparency, new data breach reporting rules have taken effect for various financial institutions. Since May 13, 2024, non-banking financial institutions, including mortgage brokers, payday lenders, and tax preparation firms, must report data breaches to the Federal Trade Commission (FTC) within 30 days of discovery. This new mandate, part of the FTC's Safeguards Rule, expands the breach notification requirements to a broader range of financial entities not overseen by the Securities and Exchange Commission (SEC).
Furthermore, by June 15, 2024, smaller reporting companies—those with a public float under $250 million or annual revenues under $100 million—must comply with the SEC’s new cybersecurity incident reporting rules, aligning their disclosure obligations with those of larger corporations. These changes mark a significant step towards enhancing transparency and accountability in data breach reporting across the financial sector.
How Can Financial Institutions Secure Their Data?
Understanding and tracking your sensitive data is fundamental to robust data security practices. The first step in safeguarding data is detecting and classifying what you have. It's far easier to protect data when you know it exists. This allows for appropriate measures such as encryption, controlling access, and monitoring for unauthorized use. By identifying and mapping your data, you can ensure that sensitive information is adequately protected and compliance requirements are met.
Identify Sensitive Data: Data is constantly moving, which makes it a challenge to know exactly what data you have and where it resides. This includes customer information, financial records, intellectual property, and any other data deemed sensitive. Having an automated data classification tool is a crucial first step. This includes ‘shadow’ data that may not be well known or well managed.
Data Mapping: Create and maintain an up-to-date map of your data landscape. This map should show where data is stored, processed, and transmitted, and who has access to it. It helps in quickly identifying which systems and data were affected by a breach and the impact blast radius (how extensive is the damage).
"Your Data Has Been Breached, Now What?"
When a data breach occurs, the immediate response is critical in mitigating damage and addressing the aftermath effectively. The investigation phase is particularly crucial as it determines the extent of the breach, the type and sensitivity of the data compromised, and the potential impact on the organization.
A key challenge during the investigation phase is understanding where the sensitive data was located at the time of the data breach and why or how existing controls were insufficient.
Without a proper data classification process or solution in place, it is difficult to ascertain the exact locations of the sensitive data or the applicable security posture at the time of the breach within the short timeframe required by the SEC and FTC reporting rules.
Here's a breakdown of the essential steps and considerations during the investigation phase:
1. Develop Appropriate Posture Policies and Enforce Adherence:
Establish policies that alert on and can help enforce appropriate security posture and access controls - these can be out-of-the-box fitting various compliance frameworks or can be customized for unique business or privacy requirements. Monitor for policy violations and initiate appropriate remediation actions (which can include ticket issuance, escalation notification, and automated access revocation or de-identification).
2. Conduct the Investigation: Determine Data Breach Source:
Identify how the breach occurred. This could involve phishing attacks, malware, insider threats, or vulnerabilities in your systems.
According to the FTC, it is critical to clearly describe what you know about the compromise. This includes:
- How it happened
- What information was taken
- How the thieves have used the information (if you know)
- What actions you have taken to remedy the situation
- What actions you are taking to protect individuals, such as offering free credit monitoring services
- How to reach the relevant contacts in your organization
Create a Comprehensive Plan: Additionally, create a comprehensive plan that reaches all affected audiences, such as employees, customers, investors, business partners, and other stakeholders.
Affected and Duplicated Data: Ascertain which data sets were accessed, altered, or exfiltrated. This involves checking logs, access records, and utilizing forensic tools. Assess if sensitive data has been duplicated or moved to unauthorized locations. This can compound the risk and potential damage if not addressed promptly.
How Sentra Helps Automate Compliance and Incident Response
Sentra’s Data Security Posture Management solution provides organizations with full visibility into their data’s locations (including shadow data) and an up-to-date data catalog with classification of sensitive data. Sentra provides this without any complex deployment or operational work involved, this is achieved due to a cloud-native agentless architecture, using cloud provider APIs and mechanisms.
Below you can see the different data stores on the Sentra dashboard.

Sentra Makes Data Access Governance (DAG) Easy
Sentra helps you understand which users have access to what data and enrich metadata catalogs for comprehensive data governance. The accurate classification of cloud data provides advanced classification labels, including business context regarding the purpose of data, and automatic discovery, enabling organizations to gain deeper insights into their data landscape. This both enhances data governance while also providing a solid foundation for informed decision-making.
Sentra's detection capabilities can pinpoint over permissioning to sensitive data, prompting organizations to swiftly control them. This proactive measure not only mitigates the risk of potential breaches but also elevates the overall security posture of the organization by helping to institute least-privilege access.
Below you can see an example of a user’s access and privileges to which sensitive data.

Breach Reporting With Sentra
Having a proper classification solution helps you understand what kind of data you have at all times.
With Sentra, it's easier to pull the information for the report and understand whether there was sensitive data at the time of breach, what kind of data there was, and who/what had access to it, in order to have an accurate report.

To learn more about how you can gain full coverage and an up-to-date data catalog with classification of sensitive data, schedule a live demo with our experts.
<blogcta-big>

Key Practices for Responding to Compliance Framework Updates
Key Practices for Responding to Compliance Framework Updates
Most privacy, IT, and security teams know the pain of keeping up with ever-changing data compliance regulations. Because data security and privacy-related regulations change rapidly over time, it can often feel like a game of “whack a mole” for organizations to keep up. Plus, in order to adhere to compliance regulations, organizations must know which data is sensitive and where it resides. This can be difficult, as data in the typical enterprise is spread across multiple cloud environments, on premises stores, SaaS applications, and more. Not to mention that this data is constantly changing and moving.
While meeting a long list of constantly evolving data compliance regulations can seem daunting, there are effective ways to set a foundation for success. By starting with data security and hygiene best practices, your business can better meet existing compliance requirements and prepare for any future changes.
Recent Updates to Common Data Compliance Frameworks
The average organization comes into contact with several voluntary and mandatory compliance frameworks related to security and privacy. Here’s an overview of the most common ones and how they have changed in the past few years:
Payment Card Industry Data Security Standard (PCI DSS)
What it is: PCI DSS is a set of over 500 requirements for strengthening security controls around payment cardholder data.
Recent changes to this framework: In March 2022, the PCI Security Standards Council announced PCI DSS version 4.0. It officially went into effect in Q1 2024. This newest version has notably stricter standards for defining which accounts can access environments containing cardholder data and authenticating these users with multi-factor authentication and stronger passwords. This update means organizations must know where their sensitive data resides and who can access it.
U.S. Securities and Exchange Commission (SEC) 4-Day Disclosure Requirement
What it is: The SEC’s 4-day disclosure requirement is a rule that requires more established SEC registrants to disclose a known cybersecurity incident within four business days of its discovery.
Recent changes to this framework: The SEC released this disclosure rule in December 2023. Several Fortune 500 organizations had to disclose cybersecurity incidents, including a description of the nature, scope, and timing of the incident. Additionally, the SEC requires that the affected organization release which assets were impacted by the incident. This new requirement significantly increases the implications of a cyber event, as organizations risk more reputational damage and customer churn when an incident happens.
In addition, the SEC will require smaller reporting companies to comply with these breach disclosure rules in June 2024. In other words, these smaller companies will need to adhere to the same breach disclosure protocols as their larger counterparts.
Health Insurance Portability and Accountability Act (HIPAA)
What it is: HIPPA safeguards that protect patient information through stringent disclosure and privacy standards.
Recent changes to this framework: Updated HIPAA guidelines have been released recently, including voluntary cybersecurity performance goals created by the U.S. Department of Health and Human Services (HHS). These recommendations focus on data security best practices such as strengthening access controls, implementing incident planning and preparedness, using strong encryption, conducting asset inventory, and more. Meeting these recommendations strengthens an organization’s ability to adhere to HIPAA, specifically protecting electronic protected health information (ePHI).
General Data Protection Regulation (GDPR) and EU-US Data Privacy Framework
What it is: GDPR is a robust data privacy framework in the European Union. The EU-US Data Privacy Framework (DPF) adds a mechanism that enables participating organizations to meet the EU requirements for transferring personal data to third countries.
Recent changes to this framework: The GDPR continues to evolve as new data privacy challenges arise. Recent changes include the EU-U.S. Data Privacy framework, enacted in July 2023. This new framework requires that participating organizations significantly limit how they use personal data and inform individuals about their data processing procedures. These new requirements mean organizations must understand where and how they use EU user data.
National Institute of Standards and Technology (NIST) Cybersecurity Framework
What it is: NIST is a voluntary guideline that provides recommendations to organizations for managing cybersecurity risk. However, companies that do business with or a part of the U.S. government, including agencies and contractors, are required to comply with NIST.
Recent changes to this framework: NIST recently released its 2.0 version. Changes include a new core function, “govern,” which brings in more leadership oversight. It also highlights supply chain security and executing more impactful cyber incident responses. Teams must focus on gaining complete visibility into their data so leaders can fully understand and manage risk.
ISO/IEC 27001:2022
What it is: ISO/IEC 27001 is a certification that requires businesses to achieve a level of information security standards.
Recent changes to this framework: ISO 27001 was revised in 2022. While this addendum consolidated many of the controls listed in the previous version, it also added 11 brand-new ones, such as data leakage protection, monitoring activities, data masking, and configuration management. Again, these additions highlight the importance of understanding where and how data gets used so businesses can better protect it.
California Consumer Privacy Act (CCPA)
What it is: CCPA is a set of mandatory regulations for protecting the data privacy of California residents.
Recent changes to this framework: The CCPA was amended in 2023 with the California Privacy Rights Act (CPRA). This new edition includes new data rights, such as consumers’ rights to correct inaccurate personal information and limit the use of their personal information. As a result, businesses must have a stronger grasp on how their CA users’ data is stored and used across the organization.
2024 FTC Mandates
What it is: The Federal Trade Commission (FTC)’s new mandates require some businesses to disclose data breaches to the FTC as soon as possible — no later than 30 days after the breach is discovered.
Recent changes to this framework: The first of these new data breach reporting rules is the Standards for Safeguarding Customer Information (Safeguards Rule) which took effect in May 2024. The Safeguards Rule puts disclosure requirements on non-banking financial institutions and financial institutions that aren’t required to register with the SEC (e.g, mortgage brokers, payday lenders, and vehicle dealers).
Key Data Practices for Meeting Compliance
These frameworks are just a portion of the ever-changing compliance and regulatory requirements that businesses must meet today. Ultimately, it all goes back to strong data security and hygiene: knowing where your data resides, who has access to it, and which controls are protecting it.
To gain visibility into all of these areas, businesses must operationalize the following actions throughout their entire data estate:
- Discover data in both known and unknown (shadow) data stores.
- Accurately classify and organize discovered data so they can adequately protect their most sensitive assets.
- Monitor and track access keys and user identities to enforce least privilege access and to limit third-party vendor access to sensitive data.
- Detect and alert on risky data movement and suspect activity to gain early warning into potential breaches.
Sentra enables organizations to meet data compliance requirements with data security posture management (DSPM) and data access governance (DAG) that travel with your data. We help organizations gain a clear view of all sensitive data, identify compliance gaps for fast resolution, and easily provide evidence of regulatory controls in framework-specific reports.
Find out how Sentra can help your business achieve data and privacy compliance requirements.
If you want to learn more, request a demo with our data security experts.

How PCI DSS 4.0 Improves Your Security Posture
How PCI DSS 4.0 Improves Your Security Posture
The release of PCI DSS 4.0 marks a fundamental shift in how organizations are expected to protect payment card data. Compliance is no longer about passing periodic audits or maintaining static controls, it now requires a continuous, risk-based approach to securing cardholder data, especially in cloud and third-party environments.
With expanded requirements, increased focus on cloud service providers, and 51 future-dated controls becoming mandatory by March 31, 2025, organizations that store, process, or transmit cardholder data must rethink how they approach PCI compliance. Traditional, point-in-time methods struggle to keep up with dynamic cloud data, shadow PAN, and evolving access patterns.
In this blog, we break down the most important changes in PCI DSS 4.0, explain what the March 2025 deadline really means, and show how organizations can operationalize PCI compliance through continuous visibility, monitoring, and protection of sensitive payment card data.
Understanding PCI DSS v4.0
PCI DSS v4.0 brings several notable updates, emphasizing a more comprehensive and risk-based approach to data security. Companies in the payment card ecosystem must take note of these changes to ensure they remain compliant and resilient against evolving threats.
Increased Focus on Cloud and Service Providers
One of the key highlights of PCI DSS v4.0 is its focus on cloud environments and third-party service providers. As more businesses leverage cloud services for storing and processing payment data, it's imperative to extend security controls to these environments.
Expanded Scope of Requirements
With the proliferation of digital transactions, PCI DSS v4.0 expands the scope of requirements to address emerging technologies and evolving threats. The standard now covers a broader range of systems, applications, and processes involved in payment card transactions.
Emphasis on Risk-Based Approach
Recognizing that not all security threats are created equal, PCI DSS v4.0 places a greater emphasis on a risk-based approach to security. Organizations should assess risks systematically and prioritize security measures based on potential impact and likelihood of occurrence.
Enhanced Focus on Data Protection
From encryption and access control to data retention policies, organizations are expected to implement robust measures to prevent unauthorized access and data breaches. This will help mitigate the risk of data theft and ensure compliance with regulatory standards.
New PCI DSS 4.0 Release Implementation by March 2025
Out of the 64 of the new requirements, 51 are future dated due to their complexity and/or cost of implementation. This is relevant and important for any business that stores, processes or transmits cardholder data.
Further, it is crucial to focus on establishing a continuous process:
- Automated log analysis for threat detection (Req: 10.4.1.1)
- On-going review of access to sensitive data (Req: 7.2.4)
- Detection of stored PAN anywhere it is not expected (Req: 12.10.7)
How Sentra Helps Comply With PCI DSS 4.0
Below are a few examples of how Sentra can assist you in complying with PCI DSS 4.0 by continuously monitoring your environment for threats and vulnerabilities.
In today's threat landscape, security is an ongoing process. PCI DSS v4.0 emphasizes the importance of continuous monitoring and testing to detect and respond to security incidents in real-time. By implementing automated monitoring tools and conducting regular security assessments, organizations can proactively identify vulnerabilities and address them before they are exploited by attackers.
| PCI DSS 4.0 New Requirement | How Sentra Solves It |
|---|---|
| 10.4.1.1 Automated mechanisms are used to perform audit log reviews. | Sentra's Data Detection and Response (DDR) module continuously monitors logs from sensitive data stores, identifying threats and anomalies in real time that may indicate potential data breaches or unauthorized access to sensitive data. |
|
7.2.4 All user accounts and related access privileges, including third party/vendor accounts, are reviewed as follows:
|
Sentra's Data Security Posture Management (DSPM) data access module frequently scans your sensitive data stores, mapping out the various identities with access to your data, including third-party entities, internal users, and applications. This aids in ensuring least privilege access and allows for the analysis of each identity's security posture through a risk-based approach. |
|
12.10.7 Incident response procedures are in place, to be initiated upon the detection of stored PAN anywhere it is not expected, and include:
|
Sentra's scanning and classification engine detects all types of sensitive data, including PII, digital identities, and financial data, especially PAN, across all your cloud accounts. It highlights potential "shadow data" suspected of being misplaced. Additionally, Sentra's DataTreks module tracks the movement of sensitive data across accounts, regions, and environments, helping you understand the root cause and take preventive steps. |
Use Sentra's Reporting Capabilities to Adhere With PCI DSS
Here you can see a detected S3 bucket which contains credit card numbers and personal information which are not properly encrypted.

This is an example of how Sentra creates a threat in real time, detecting suspicious activity in a sensitive AWS S3 bucket.

In the dashboard below, you can see open security issues grouped by different compliances frameworks.

Proactive Integration of New Compliance Controls
Sentra remains vigilant in staying up to date with changes in PCI-DSS, GDPR, CCPA and other compliance frameworks. To ensure continuous compliance and security, Sentra actively monitors updates and integrates new controls as they become available. This proactive approach allows users to automate the validation process on an ongoing basis, ensuring that they always adhere to the latest standards and maintain a robust security posture.
Implementation Timeline and Best Practices
It's essential for relevant companies to understand the implementation timeline for PCI DSS v4.0. With a two-phase approach, certain requirements are future-dated due to their complexity or cost of implementation. However, it's crucial not to overlook these future requirements, as they will eventually become mandatory for compliance.
These requirements will be considered best practices until March 31, 2025, after which they will become obligatory. This transition period allows organizations to gradually adapt to the new standards while ensuring they meet current compliance requirements.
Conclusion
PCI DSS 4.0 represents a clear move away from checkbox compliance toward continuous protection of cardholder data. As the payment card industry continues to evolve, so must the security measures used to protect sensitive data. PCI DSS v4.0 represents a significant step forward in enhancing data security and resilience against emerging threats. Understanding the key changes and implementation timeline is crucial for companies to proactively adapt to the new standard and maintain compliance in an ever-changing regulatory landscape.
Sentra plays a pivotal role in this ongoing compliance effort. Its comprehensive features align closely with the requirements of PCI DSS v4.0, providing automated log analysis for threat detection, ongoing review of access to sensitive data, and detection of stored PAN outside expected locations. Through Sentra's Data Detection and Response (DDR) module, organizations can continuously monitor logs from sensitive data stores, identifying threats and anomalies in real-time, thus aiding in compliance with PCI DSS 4.0 requirements such as automated log reviews.
Furthermore, Sentra's Data Security and Posture Management (DSPM) module facilitates the review of user accounts and access privileges, ensuring that access remains appropriate based on job function and addressing any inappropriate access, in line with PCI DSS v4.0 requirements. In addition, Sentra's scanning and classification engine, coupled with its DataTreks module, assists in incident response procedures by detecting all types of sensitive data, including PAN, across cloud accounts and tracking the movement of sensitive data, aiding in the remediation of data leaks or process gaps.
By leveraging these capabilities, organizations can streamline their compliance efforts, mitigate risks, and maintain the security and integrity of cardholder data in accordance with PCI DSS v4.0 requirements.
<blogcta-big>

Navigating the SEC's New Cybersecurity and Incident Disclosure Rules
Navigating the SEC's New Cybersecurity and Incident Disclosure Rules
Recently, the U.S Securities and Exchange Commission (SEC) had adopted stringent cybersecurity and incident disclosure rules, placing a heightened emphasis on the imperative need for robust incident detection, analysis, and reporting processes.
Following these new rules, public companies are finding themselves under a microscope, obligated to promptly disclose any cybersecurity incident deemed material. This disclosure mandates a detailed account of the incident's nature, scope, and timing within a stringent 4-business-day window. In essence, companies are now required to offer swift detection, thorough analysis, and the delivery of a comprehensive report on the potential impact of a data breach for shareholders and investors.
SEC's Decisive Actions in 2023: A Wake-Up Call for CISOs
The SEC's resolute stance on cybersecurity became clear with two major actions in the latter half of 2023. In July, the SEC implemented rules, effective December 18, mandating the disclosure of "material" threat/breach incidents within a four-day window. Simultaneously, annual reporting on cybersecurity risk management, strategy, and governance became a new norm. These actions underscore the SEC's commitment to getting tough on cybersecurity, prompting Chief Information Security Officers (CISOs) and their teams to broaden their focus to the boardroom. The evolving threat landscape now demands a business-centric approach, aligning cybersecurity concerns with overarching organizational strategies.
Adding weight to the SEC's commitment, in October, SolarWinds Corporation and its CISO, Timothy G. Brown was charged with fraud and internal control failures relating to allegedly known cybersecurity risks and vulnerabilities. This marked a historic moment, as it was the first time the SEC brought cybersecurity enforcement claims against an individual. SolarWinds' case, where the company disclosed only "generic and hypothetical risks" while facing specific security issues, serves as a stark reminder of the SEC's intolerance towards non-disclosure and intentional fraud in the cybersecurity domain. It's evident that the SEC's cybersecurity mandates are reshaping compliance norms.
This blog will delve into the intricacies of these rules, their implications, and how organizations, led by their CISOs, can proactively meet the SEC's expectations.
Implications for Compliance Professionals
Striking the Balance: Over-Reporting vs. Under-Reporting
Compliance professionals must navigate the fine line between over-reporting and under-reporting, a task akin to a high-stakes tightrope walk.
Over-Reporting: The consequences of hyper-vigilance can't be underestimated. Reporting every incident, regardless of its material impact, might instigate unwarranted panic in the market. This overreaction could lead to a domino effect, causing a downturn in stock prices and inflicting reputational damage.
Under-Reporting: On the flip side, failing to report within the prescribed time frame has its own set of perils. Regulatory penalties loom large, and the erosion of investor trust becomes an imminent risk. The SEC's strict adherence to disclosure timelines emphasizes the need for precision and timeliness in reporting.
Market Perception
Shareholder & Investor Trust: Balancing reporting accuracy is crucial for maintaining shareholder and investor trust. Over-reporting may breed skepticism and lead to potential divestment, while delayed reporting can erode trust and raise questions about the organization's cybersecurity commitment.
Regulatory Compliance: The SEC mandates timely and accurate reporting. Failure to comply incurs penalties, impacting both finances and the organization's regulatory standing. Regulatory actions, combined with market fallout, can significantly affect the long-term reputation of the organization.
Strategies for Success
The Day Before - Minimize the Impact of the Data Breach
To effectively minimize the impact of a data breach, the first and most critical step is understanding where your sensitive data resides. By identifying, mapping, and properly classifying this data within your environment, you establish the foundation for strong protection and informed risk mitigation.
Data Security Posture Management (DSPM) solutions strengthen this foundation by providing continuous visibility, analysis, and reinforcement of your data security posture. With DSPM, organizations can confidently safeguard sensitive information in the face of evolving threats by enabling the ability to:
- Discovers any piece of data you have and classifies the different data types in your organization.
- Automatically detects the risks of your sensitive data (including data movement) and remediation.
- Aligns your data protection practices with security regulations and best practices. Incorporates compliance measures for handling personally identifiable information (PII), protected health information (PHI), credentials, and other sensitive data.
From encryption to access controls, adopting a comprehensive security approach safeguards your organization against potential breaches. It’s crucial to conduct a thorough risk assessment to measure vulnerabilities and potential threats to your data. Understanding the risks allows for targeted and proactive risk management strategies.

The Day After: Maximizing the Pace to Handle the Impact (reputation, money, recovery, etc)
In the aftermath of a breach, having a “Data Catalog” with data sensitivity ranking helps with understanding the materiality of the breach and quick resolution and reporting within the 4-day window.
Swift incident response is also paramount; and this can be accomplished by establishing a rapid plan for mitigating the impact on reputation, finances, and overall recovery. This is where the data catalog comes into play again, by helping you understand which data was extracted, facilitating quick and accurate resolution. The next step for the ‘day after’ is actively managing your organization's reputation post-incident through transparent communication and decisive action, which contributes to trust and credibility rebuilding.

Finally, always conduct a comprehensive post-incident analysis for valuable insights, and enhance future security measures through a continuous improvement cycle. Building resilience into your cybersecurity framework by proactively adapting and fortifying defenses, best positions your organization to withstand future challenges. Adhering to these strategies enables organizations to navigate the cybersecurity landscape effectively, minimizing risks, ensuring compliance, and enhancing their ability to respond swiftly to potential incidents.
Empowering Compliance in the Face of SEC Regulations with Sentra’s DSPM
Sentra’s DSPM solution both discovers and classifies sensitive data, and aligns seamlessly with SEC's cybersecurity and incident disclosure rules. The real-time monitoring swiftly identifies potential breaches, offering a critical head start within the 4-day disclosure window.
Efficient impact analysis enables compliance professionals to gauge materiality and consequences for shareholders during reporting. Sentra's DSPM streamlines incident analysis processes, adapting to each organization's needs. Having a "Data Catalog" aids in understanding breach materiality for quick resolution and reporting, while detailed reports ensure SEC compliance.
By integrating Sentra, organizations meet regulatory demands, fortify data security, and navigate evolving compliance requirements. As the SEC shapes the cybersecurity landscape, Sentra guides towards a future where proactive incident management is a strategic imperative.
To learn more, schedule a demo with one of our experts.
<blogcta-big>

Manage Data Security and Compliance Risks with DSPM - A Deep Dive into Common Data Regulations
Manage Data Security and Compliance Risks with DSPM - A Deep Dive into Common Data Regulations
Cloud innovation necessitates migrating more workloads to the cloud, creating an exponential increase in data volume. As a result, data proliferation and sprawl make it almost impossible to gain the right visibility into the cloud infrastructure to identify sensitive data and its security posture. What’s more, data owners constantly load and move data, while security analysts and compliance officers have the responsibility to enforce regulations and monitor these actions. This dynamic presents challenges for data security professionals and Governance, Risk, and Compliance (GRC) teams in managing complex compliance requirements across different regulatory frameworks.
Understanding and accurately classifying cloud data is a critical foundational step towards maintaining a stable compliance posture against regulatory compliance framework benchmarks.
Here are a few examples of how DSPM, with its advanced and granular visibility into complex cloud environments, can help enterprises to efficiently detect sensitive data and accurately quantify the data risk:
- Not all sensitive data resides in data stores: Data is scattered across various services from different vendors, including managed cloud services, containerized environments, SaaS services, and hosted cloud drives. DSPM has the ability to detect and classify data at the most granular level (including tables and objects). This ensures that no sensitive data is left undetected, when monitoring for compliance gaps.
- Defining data classes plays a pivotal role in quantifying data compliance risks: Accurate classification means having very clearly categorized data classes that relate to the relevant compliance frameworks. A scenario in which multiple data classes reside in a single data store, will expand the data attack surface, raising the risk score. For instance, a database might contain Social Security Numbers (SSNs) and Personal Addresses, or Credit Card Numbers and CVVs. Such data stores are often replicated and moved between production and development environments, and their log files may contain sensitive information. That’s why DSPM is an invaluable tool to proactively scan and detect these issues on an ongoing basis.
- Always track the security posture of your data stores: For instance, keeping PCI data outside of your PCI compliant environment or storing PII data outside of the designated region could create vulnerabilities. This often happens when a testing or debugging environment is created from production data.
Lets take a look at the specific requirements of some common compliance frameworks and how DSPM will automatically discover, classify, quantify the data risk and alert on issues to maintain a strong and stable compliance posture.
PCI-DSS
The Payment Card Industry Data Security Standard (PCI DSS) comprises security protocols created to guarantee the secure handling of credit card information by companies engaged in acceptance, processing, storage, or transmission of such data.
Here are some of the issues that a DSPM platform will proactively detect, to support the PCI-DSS requirements of safeguarding cardholder data and implementing robust access control measures to fortify the security environment:
- Identify inadvertent leaks of Primary Account Numbers (PAN) into log files
- Detect instances where PAN lacks proper encryption at rest or is stored without being masked
- Pinpoint the storage locations of encryption keys, ensuring that they are not stored in undesignated areas
- Prevent unauthorized access to PCI data
GDPR
GDPR, a regulation created to safeguard the privacy of EU citizen data, sets stringent standards applicable to both EU and non-EU organizations. It mandates adherence to principles such as data minimization, requiring organizations to collect only the necessary data for their declared purposes. Additionally, GDPR demands the timely correction, deletion, or termination of inaccurate data and imposes restrictions on the duration of data retention. Organizations must ensure data protection, privacy, and the ability to substantiate GDPR compliance.
Here is how DSPM proves instrumental in aligning with GDPR requirements:
- Detect Personally Identifiable Information (PII) stored across various cloud accounts, datastores and SaaS providers
- Ensure adherence to the 'Data Minimization Principle' by enabling access to authorized users only
- Proactively alert organizations to instances where sensitive data lacks safeguards against potential loss or theft
- Ensure all regulated data meets the specified data retention and auditing requirements
HIPAA
HIPAA, the Health Insurance Portability and Accountability Act, is a United States compliance framework designed to safeguard the health information of patients. Covering privacy, security, breach notifications, and enforcement rules, HIPAA imposes strict regulations on Protected Health Information (PHI), encompassing identifiable details such as names, addresses, birthdates, Social Security Numbers (SSNs), and medical records. Guidelines include implementing access control, audit control, integrity control, and transmission security for electronic PHI. Electronic Health Record (EHR) systems, considered the future of medical records, must adhere to all security rules and HIPAA guidelines.
This is how DSPM is indispensable in achieving HIPPA compliance:
- Identify all Protected Health Information (PHI) stored in cloud accounts, including patient identifying details such as names, addresses, birthdates, SSNs, phone numbers, test results, and health insurance information
- Scan various data repositories to locate stored PHI, including managed databases, structured files, documents, and scanned images
- Ensure all data storage for PHI has proper access control, logging, backups, and security measures to prevent unauthorized access, loss, or theft
DSPM's advanced visibility into the entire multi-cloud data estate, combined with its classification accuracy, ensures no data is overlooked, even at the most granular level, automatically strengthening compliance posture and readiness.

Here you can see how Sentra measures an organization’s compliance posture in relation to industry benchmarks.
To learn more, book a demo and talk to a DSPM expert.

GDPR Audit Evidence Without the Fire Drill: How to Build a Trusted, Provable Compliance Posture
GDPR Audit Evidence Without the Fire Drill: How to Build a Trusted, Provable Compliance Posture
Modern privacy and security leaders don’t fail GDPR audits because they lack controls. They struggle because they can’t prove those controls quickly and consistently, across all the places regulated data lives. If every GDPR audit still feels like a fire drill; chasing spreadsheets, screenshots, and point‑in‑time exports. It’s a sign you’re missing a trusted, provable compliance posture for regulated data.
This article walks through:
- What GDPR auditors actually care about
- Why spreadsheets and legacy tools break down at scale
- How to build a live, unified view of regulated data and its controls
- A practical path to make audits predictable (and much less painful)
Throughout, we’ll focus on a specific outcome:
Making it easy for security, GRC, and privacy teams to prove control over regulated data and pass audits with minimal overhead.
What GDPR Auditors Actually Ask For
Nearly every GDPR audit eventually boils down to three questions:
- Where is regulated personal data stored?
Across cloud accounts, SaaS apps, on‑prem databases, and file shares; PII, PHI, PCI, and other regulated categories.
- Who can access it, and under what conditions?
Which identities, roles, and services can reach which data sets, and whether basic protections like encryption, backup, and logging are consistently applied.
- Can you produce trustworthy evidence, aligned to the framework?
Inventory exports, control posture summaries, and data‑store reports that clearly tie regulated data to the controls in place; ideally mapped to GDPR articles and related frameworks (SOC 2, PCI‑DSS, HIPAA, etc.).
If you can’t answer these questions quickly, consistently, and from a single source of truth, you’re always one personnel change or one missed export away from an audit scramble.
Why Spreadsheets and Point Tools Don’t Scale
Many organizations start with:
- CMDBs and manual data inventories
- Privacy catalogs for RoPA and DSAR workflows
- Legacy discovery tools built for on‑prem or single‑cloud environments
At small scale, this can work. But as regulated data expands across multi‑cloud, SaaS, and hybrid estates, several problems emerge:
Fragmented views: One tool knows about databases, another knows about M365/Google Workspace, another about SaaS; none shows the full regulated‑data picture.
Static exports: Evidence lives in CSVs and screenshots that are stale minutes after they’re generated.
Control blind spots: Security posture tools see misconfigurations, but not which ones actually matter for GDPR‑covered data.
High human overhead: Every new audit, business unit, or regulator request spins up a new spreadsheet.
The result: smart people spending weeks cross‑referencing exports instead of improving controls.
What a “Trusted, Provable Compliance Posture” Looks Like
To get out of fire‑drill mode, you need a living, data‑centric foundation for GDPR evidence:
- Unified, high‑accuracy regulated‑data inventory
- Discovery and classification of regulated data across cloud, SaaS, and on‑prem, not just one stack.
- Consistent data classes for PII/PHI/PCI and industry‑specific artifacts (finance, HR, healthcare, IP, etc.)
- Continuous control checks around that data
- Encryption, backup, access controls, logging, and other protections evaluated in context of the data they protect, reported as compliance posture signals rather than raw misconfigurations.
- Audit‑ready, framework‑aligned reporting
- Pre‑built GDPR and related report templates that pull from the same underlying inventory and posture engine, so evidence is consistent across audits and stakeholders.
- Shared visibility for Security, GRC, and Privacy
- Security sees risk and controls; GRC sees framework mappings; Privacy sees DSAR and data‑subject context; all using the same underlying data catalog and posture engine.
When these pieces are in place, you move from “rebuilding” evidence for every audit to proving an already‑known posture with low incremental effort.
How Sentra Helps You Get There
Sentra is designed as a data‑first security and compliance platform that sits on top of your cloud, SaaS, and on‑prem environments and focuses specifically on regulated data. Key capabilities for GDPR:
- Unified discovery & classification of regulated data
Sentra builds a single catalog of PII/PHI/PCI and other regulated data across your multi‑cloud, SaaS, and on‑prem landscape, powered by high‑accuracy, AI‑driven classification.
- Access mapping and control posture
It maps which identities can access which sensitive stores, and continuously evaluates encryption, backup, access, and logging posture around those stores, surfacing issues as prioritized signals instead of isolated misconfigurations.
- Next‑gen, audit‑ready reporting
Sentra’s reporting layer generates GDPR‑aligned PDF reports, inventory CSVs, and posture summaries that non‑technical GRC, legal, and auditor stakeholders can consume directly.
Together, these capabilities give you exactly what GDPR reviewers expect to see without manual collation every time.
A Practical Three‑Step Path to GDPR Confidence
You don’t need a multi‑year transformation to get started. Most teams can make visible progress in a few phases:
- Catalog high‑value GDPR domains
- Prioritize key regions, business units, and platforms (e.g., EU customer data in AWS + M365).
- Use DSPM tooling to build a unified regulated‑data inventory across those estates.
- Attach control posture and ownership
- Connect encryption, backup, access, and logging signals directly to each regulated data store.
- Identify clear owners and remediation paths for misaligned controls.
- Standardize evidence workflows
- Move from ad‑hoc exports to standardized GDPR (and multi‑framework) reports generated from the same underlying catalog and posture views.
- Train Security, GRC, and Privacy teams to pull the same reports and speak from the same “source of truth” during audits.
The outcome is more than just a smoother audit. You achieve a trusted, provable compliance posture that reduces risk, accelerates evidence collection, and frees your teams to focus on better controls, not better spreadsheets.
Where to Go Next
If your last GDPR audit felt more chaotic than it should have, that’s often a signal that your regulated-data posture isn’t yet something you can demonstrate confidently on demand. Compliance shouldn’t depend on last-minute spreadsheets, manual sampling, or cross-team scrambling. It should be measurable, repeatable, and defensible at any point in time.
A focused proof of value with a modern DSPM platform can quickly surface how much regulated data you actually hold and where it resides, highlight gaps or inconsistencies in existing controls, and clarify what GDPR-aligned evidence could look like in practice - without the fire drill. The goal isn’t just passing the next audit, but building a posture you can continuously prove.

EU-US Data Privacy Framework 101
EU-US Data Privacy Framework 101
Who Does This Framework Apply To?
The EU-US Data Privacy Framework applies to any company with a branch in the EU, no matter where the data is actually processed. This means the company needs to follow the framework's rules if it handles personal information while operating in the EU.
Additionally, US companies can become part of the framework by adhering to a comprehensive set of privacy obligations related to the General Data Protection Regulation (GDPR). This inclusivity extends to data transfers from any public or private entity in the European Economic Area (EEA) to US companies that are participants in the EU-US Data Privacy Framework.
Notably, the enforcement of this framework falls under the jurisdiction of the U.S. Federal Trade Commission, endowing it with the authority to ensure compliance and uphold the specified privacy standards. This dual jurisdictional approach reflects a commitment to fostering secure and compliant data transfers between the EU and the US, promoting transparency and accountability in the handling of personal data.
Self Assessment Process
The Self-Assessment Process involves organizations certifying their adherence to the principles of the EU-U.S. Data Privacy Framework directly to the department. Successful entry into the EU-US DPF requires full compliance with these principles.
Additionally, organizations participating in the framework must be subject to the investigatory and enforcement powers of the Federal Trade Commission. This self-assessment mechanism and regulatory oversight ensure a commitment to upholding and enforcing the privacy principles outlined in the EU-US Data Privacy Framework.
Next Steps
The EU-U.S. Data Privacy Framework will undergo periodic assessments, conducted collaboratively by the European Commission, representatives of European data protection authorities, and competent U.S. authorities. The inaugural review is scheduled to occur within a year of the adequacy decision's enactment. Its purpose is to ensure the full implementation of all pertinent elements within the U.S. legal framework and verify their effective functionality in practice. This commitment to regular evaluations underscores the framework's dedication to maintaining and enhancing data privacy standards over time.
How Sentra’s DSPM Addresses the EU-US Data Privacy Framework Principles
Sentra’s DSPM meets the following requirements of the EU-US Data Privacy Framework:
- Data Minimization: Collects only the personal data necessary for the specified purpose and limits access to such data within the organization.
- Purpose Limitation: Uses the collected data only for the purposes for which it was collected and for which the individual has consented. The purposes for processing data must also be clearly communicated to individuals through a privacy notice. Lastly, it is critical to follow them closely, limiting the processing of data only to the purposes stated.
- Data Integrity and Accuracy: Ensures that personal data is kept accurate and up to date.
- Encryption: Uses encryption for data in transit and at rest to protect personal data from unauthorized access or breaches.
.webp)
- Data Retention Policies: Establishes and enforces data retention policies to ensure that personal data is not kept longer than necessary.
- Security Measures: Implements comprehensive security measures to protect against unauthorized or unlawful processing and against accidental loss, destruction, or damage.
- Access Controls: Implements access controls to ensure that only authorized personnel can access personal data.
.webp)
Data Security Posture Management (DSPM)’s Pivotal Role
Data Security Posture Management (DSPM) plays a pivotal role in data security by monitoring data movements, offering essential visibility into the storage of sensitive data, thus addressing the question:
"Where is my sensitive data and how secure is it?"
Additionally, DSPM ensures the establishment of well-defined data hygiene, audit logs and retention policies, contributing to robust data protection measures. The implementation of DSPM extends further to guarantee least privilege access to sensitive data through continuous monitoring of data access and identification of unnecessary data permissions.
Real-time monitoring of data events, encapsulated in Data Detection and Response (DDR), emerges as a critical aspect, enabling the proactive detection of data threats and mitigating the risk of data breaches.
.webp)
Here you can see the Threats module in our dashboard - it allows you to identify threats in real time detected by Sentra, such as “Access from a malicious IP address to a sensitive AWS S3 bucket”, “3rd party AWS account accessed intellectual property data for the first time”, etc. to your highly sensitive data. On the right you can see which type of data is at risk. With Sentra, you can mitigate data breaches right away — before damage occurs.
Privacy Initiatives Going Forward
Another recent privacy initiative is President Biden's Executive Order to protect Americans’ sensitive data.
The Executive Order proposes protections for most personal and sensitive information, including genomic data, biometric data, personal health data, geolocation data, financial data, and certain kinds of personally identifiable information (PII). This commitment aligns with President Biden's push for comprehensive privacy legislation, reinforcing the nation's dedication to a secure and open digital landscape while safeguarding Americans from the misuse of their personal data.
This will no doubt increase pressure on US and Global institutions to more effectively identify such sensitive personal information and enforce policies to ensure compliance with any eventual sovereignty/privacy regulations (similar to European GDPR regulations). Organizations wanting to get a head start are well advised to consider data security solutions, based on DSPM, DDR, and DAG capabilities.
In particular, deploying a data security platform now will allow organizations time to assess the full exposure resident within their entire data estate (across public cloud, SaaS and premise) so they can begin to address areas of highest risk. Additionally, they can monitor for data leakage to countries outside the US, which may create liability or penalties under future regulations
Compliance, Privacy, Risk Management and other data governance functions should work with their Data Security partners toward evaluation and implementation of data security solutions that can provide the necessary visibility and controls. Going forward, we should expect further regulatory controls over personal information.
Conclusion
The EU-US Data Privacy Framework establishes a clear and standardized approach for personal data transfers between the European Union and the United States. It fosters trust and cooperation between these two economic giants, while prioritizing the privacy and security of individuals' data.
For businesses looking to engage with partners or customers across the Atlantic, the framework provides a reliable and compliant pathway. By adhering to its principles and utilizing tools like Sentra’s Data Security Posture Management (DSPM), organizations can ensure they meet the necessary data protection standards and build trust with their stakeholders.
The framework's commitment to regular assessments further emphasizes its dedication to continuous improvement and maintaining the highest standards in data privacy. As the global landscape of data protection evolves, the EU-US Data Privacy Framework serves as a valuable step forward in fostering secure and responsible data flows.
<blogcta-big>